
Ransomware attacks impact more than their target victim
Last week Kronos (now Ultimate Kronos Group (UKG)) announced that they were hit by a ransomware attack that is
Read MoreCategory: Security Operations

Last week Kronos (now Ultimate Kronos Group (UKG)) announced that they were hit by a ransomware attack that is
Read More
Ransomware is everywhere and cybercriminals are increasingly more antagonistic, demanding ever increasing ransom payments. Palo Alto Networks’ Unit 42
Read More
By 2025, it’s estimated that cybercrime will cost the world $10.5 trillion annually—a figure that includes damage and destruction
Read More
Network security is described as the implementation of technologies, processes, and protocols designed to safeguard an organization’s communications and
Read More
In a previous blog I introduced you to the malware detection capabilities of Plixer’s intelligence product. I would like
Read More
It can happen to anyone, even the most seasoned of network security personnel. You can be searching for something
Read More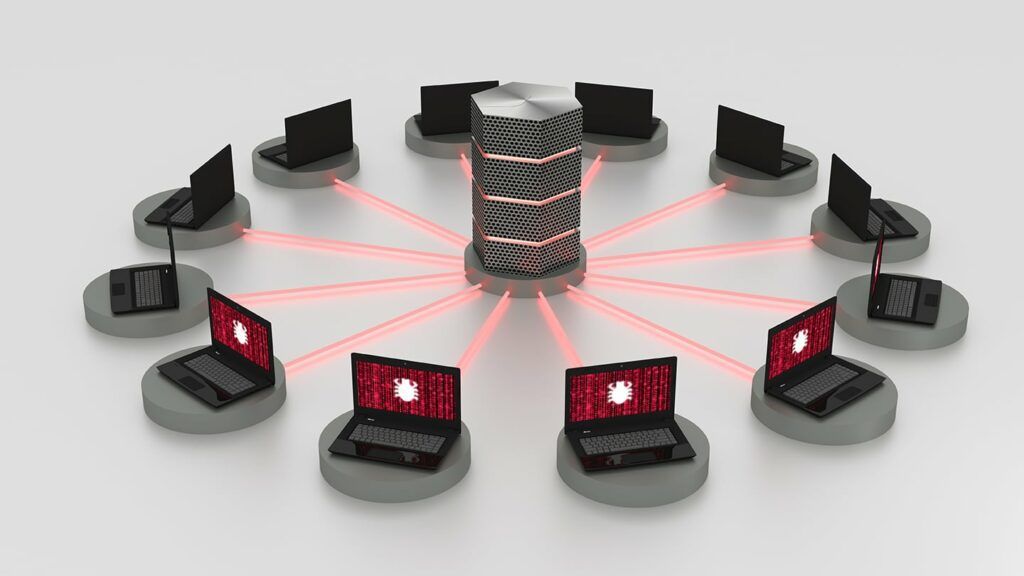
As more and more devices are added to the internet, a larger swath of insecurity comes with them. Botnets
Read More
When we hear about a cyberattack these days, there’s often a reference to when the network was originally compromised.
Read More
Last year Plixer released version 19 of Scrutinizer, and with it came the introduction of Plixer Security Intelligence, our
Read More
Imagine someone walks up to your desk and asks a very simple question: has this IP address been seen
Read More