Plixer FlowPro: DNS Analytics and Deep Packet Inspection
DNS is the first place attackers hide and the last place most teams systematically inspect. It is foundational to every connection, every application, and every user interaction. That level of trust makes it invaluable for business operations and equally attractive for adversaries looking to move quietly through environments.
FlowPro is a native capability within Plixer’s deep observability platform that functions as a purpose-built DNS analytics and threat detection tool. It gives security teams real-time visibility into DNS activity, risky lookups, and hidden indicators of compromise. When combined with Scrutinizer, DNS data becomes correlated intelligence that strengthens detection, investigation, and response across the enterprise.
Schedule a DemoDNS Analytics Powered by FlowPro + Plixer One
FlowPro inspects DNS activity directly from network traffic using deep packet inspection. It evaluates both DNS requests and responses to identify behavioral patterns and protocol-level anomalies that traditional logging methods often miss.
By analyzing traffic at the packet level, FlowPro captures context that is not available in standard DNS logs, providing more accurate visibility into how domains are being queried, resolved, and used across the network.
FlowPro detects behavioral patterns such as NXDOMAIN bursts, irregular TXT record usage, malformed responses, and abnormal query structures. These patterns are not treated as isolated events. They are normalized, enriched, and converted into IPFIX records.
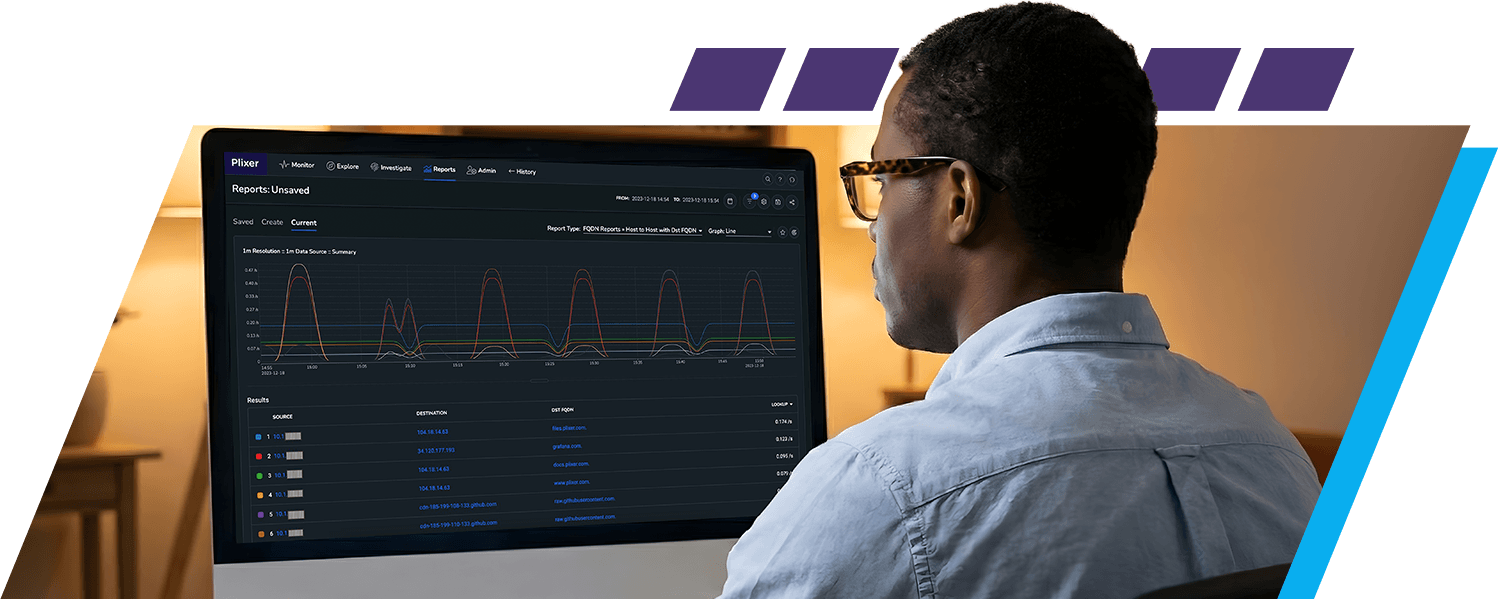
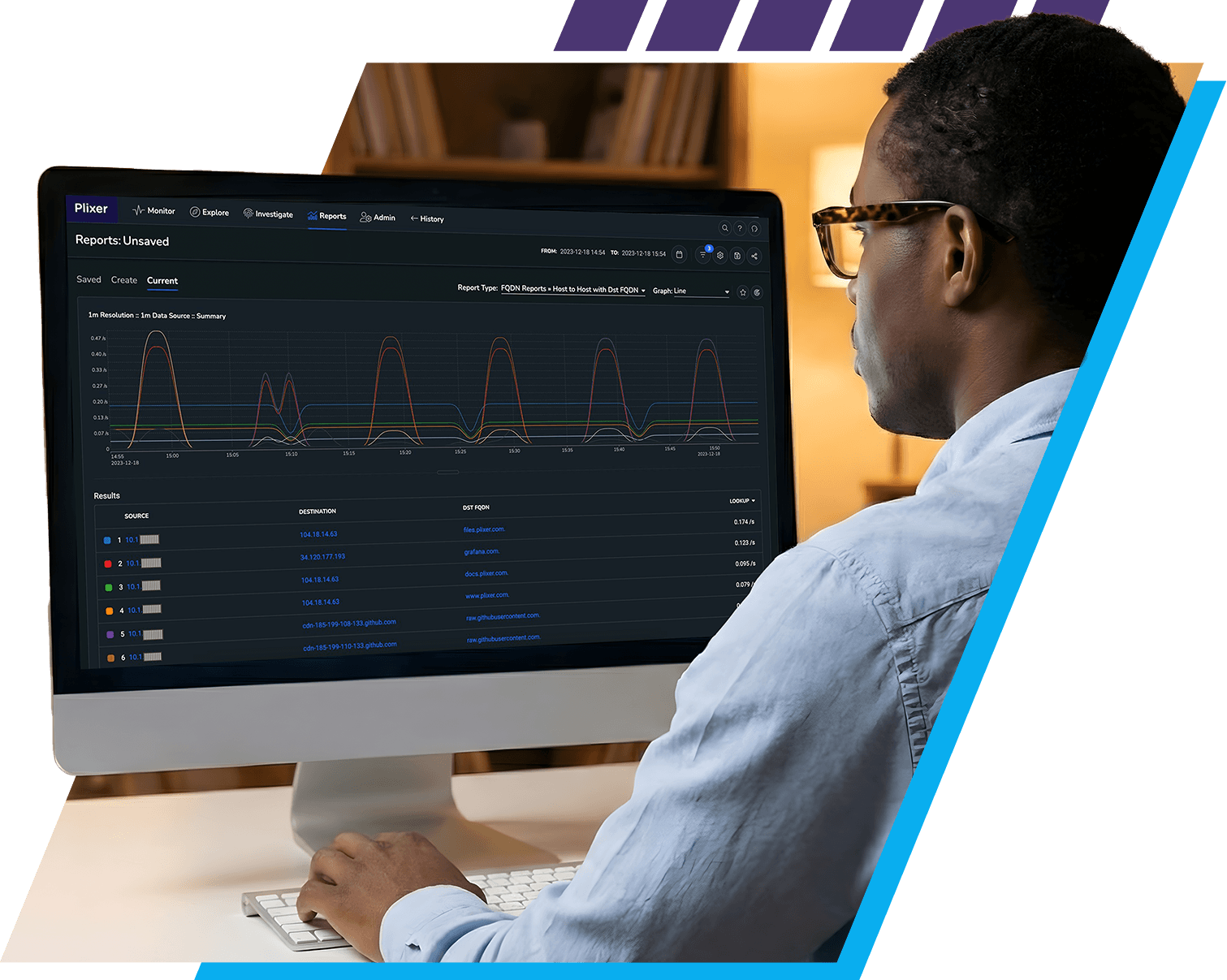
This conversion allows DNS telemetry to be handled as structured flow data. Scrutinizer receives this enriched dataset and applies enterprise-rated analytics to build context around users, hosts, applications, and services.
A modern DNS analytics and threat detection tool must provide context, not just data. FlowPro exports DNS telemetry that Plixer One correlates with broader traffic behavior and infrastructure signals. Plixer One correlates DNS metadata with east west traffic, host communication patterns, and application flows.
Security teams gain visibility into:
- Algorithmically generated domain patterns
- DNS-based data exfiltration behavior
- Command and control infrastructure activity
- Malicious domain behavior that changes over time
Why DNS Visibility Strengthens Security
Reliable threat detection depends on visibility that persists even as network architectures evolve and encryption increases. DNS provides one of the most stable sources of behavioral intelligence available to security teams and, when properly analyzed, becomes a foundation for early detection and effective response.
Schedule a DemoDNS as a Reliable Security Signal
DNS remains one of the most consistently observable protocols, even as more traffic becomes encrypted. This makes it a dependable source of behavioral signal when visibility at other layers becomes limited.
Behavior Baselines and Trend Analysis
FlowPro provides telemetry used for trend-based analytics that track DNS behavior over time. Teams can establish baselines for normal DNS activity and identify subtle deviations that may indicate early-stage threats. This improves threat hunting workflows, increases investigation accuracy, and strengthens operational confidence. A properly implemented DNS analytics and threat detection tool becomes part of core security operations rather than a supplementary data source.
FlowPro inspects DNS activity directly from network traffic using deep packet inspection. It evaluates both DNS requests and responses to identify behavioral patterns and protocol-level anomalies that traditional logging methods often miss. By analyzing traffic at the packet level, FlowPro captures context that is not available in standard DNS logs, providing more accurate visibility into how domains are being queried, resolved, and used across the network.
DNS-Based Threat Detection
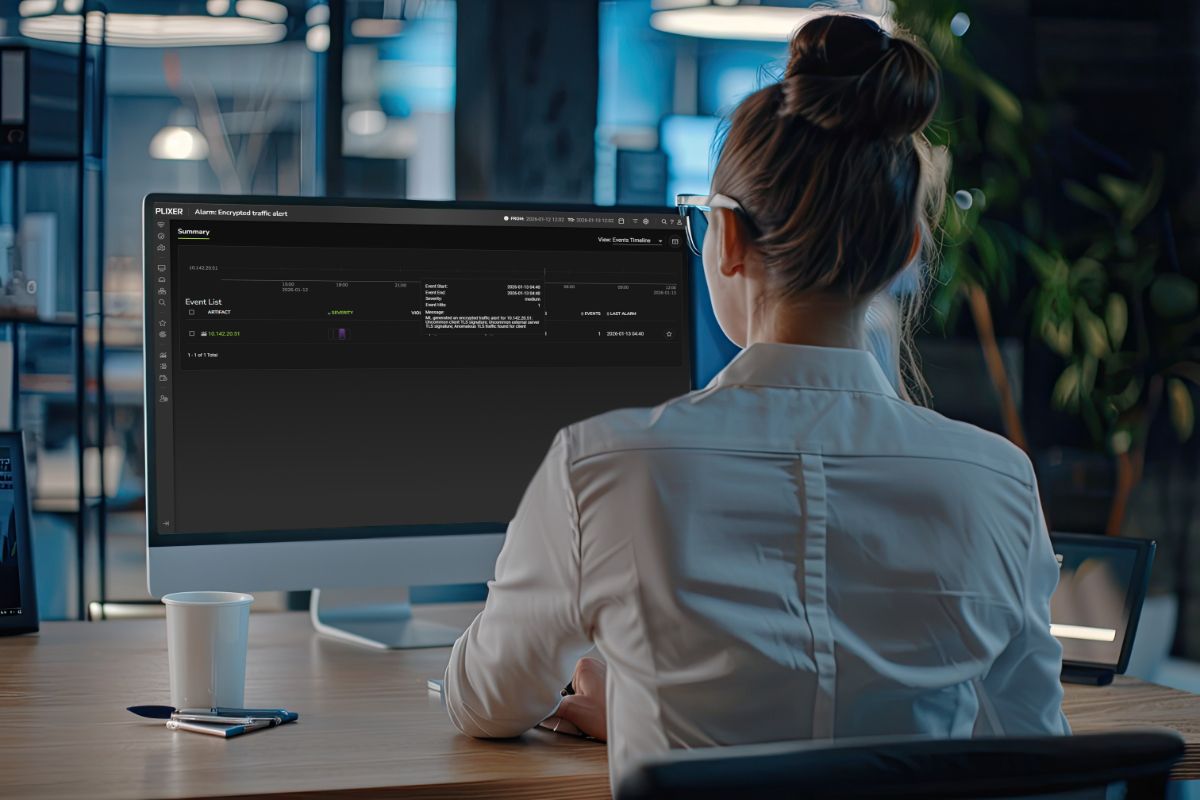
FlowPro actively identifies DNS-driven threats in real time and delivers the results through correlated analytics in Scrutinizer.
The DNS analytics and threat detection tool identifies:
- Command and control communication patterns
- DNS tunneling techniques
- Suspicious or newly weaponized domains
- Phishing infrastructure based on domain behavior
It evaluates domain entropy, query timing irregularities, and frequency patterns that are characteristic of automated malicious activity.
FlowPro flags DNS anomalies at the packet level and streams those observations to Scrutinizer. Scrutinizer correlates these signals with network flow data, user behavior, and session-level activity.
Isolated anomalies often lack impact. When aligned with unusual lateral movement or abnormal data transfer patterns, these same signals become high-confidence security events. That correlation layer is what turns FlowPro into a true DNS analytics and threat detection tool rather than a simple monitoring feature.
FlowPro also provides telemetry used for dynamic baselining of domain behavior. Domains are evaluated across time rather than being judged only by static reputation lists. This allows security teams to identify emerging infrastructure before it is widely cataloged by external feeds.
Real-time DNS detection reduces mean time to detect. Analysts are presented with structured, behavioral indicators rather than raw logs.
Scrutinizer provides visual timelines that show how DNS threats develop over time, from initial resolution attempt through follow-on traffic. This makes handoffs between SOC analysts and incident response teams faster and more reliable.
Extended operational value is created by integrating DNS threat activity into existing playbooks. Automated enrichment, tagging, and prioritization allow teams to move from detection to containment with minimal friction.
Selective Packet Capture and Forensics
Detection without evidence limits response effectiveness. FlowPro addresses investigative depth through selective packet capture.
FlowPro does not continuously capture all traffic. It activates capture only when anomalies or suspicious DNS patterns are detected. This keeps the focus on high-value telemetry while preserving system performance.
Custom flow patters can be defined for capture allowing network teams a powerful centralized troubleshooting tool and security teams an additional layer of details during hunting activities.
Captured packets can be exported to forensic tools such as Wireshark. Teams can examine DNS payloads, query structures, and response behavior in full detail.
Selective capture enables:
- Verifiable evidence of DNS tunneling
- Identification of encoded or obfuscated data
- Accurate reconstruction of DNS-based attack timelines
- Packet level detail for FlowPro threat detections
This strengthens the overall effectiveness of a DNS analytics and threat detection tool by ensuring that every alert can be supported by defensible technical evidence.
Event-driven capture significantly reduces storage and infrastructure overhead compared to continuous capture models. Investigations become more efficient because analysts do not need to filter through irrelevant traffic.
Captured DNS data can also be retained for training exercises and simulation scenarios. Teams can replay real-world DNS attack patterns to improve detection logic and response orchestration without disrupting production traffic.
DNS Analytics and Network Activity
DNS becomes significantly more valuable when paired with broader network telemetry.
TheFlowPro enriches DNS telemetry with:
- Traffic volume metrics
- Session duration data
- Host identity attributes
- Directional flow characteristics
Scrutinizer analyzes these combined datasets to reveal behavioral relationships across the environment.
A mature DNS analytics and threat detection contributes data that enables detection of:
- DNS activity tied to lateral movement
- Low bandwidth data exfiltration disguised as normal resolution traffic
- Beaconing behavior from compromised internal hosts
Multi-layer correlation allows teams to focus on intent and behavior rather than chasing isolated anomalies.
FlowPro and Scrutinizer analyze DNS behavior over extended time ranges. This allows teams to detect low-and-slow threats that operate beneath traditional thresholds.
Combined DNS and network analytics also support operational investigations. Teams can determine whether abnormal DNS behavior is the result of malicious activity or legitimate infrastructure changes. This dual-use visibility improves both security and network operations.
Scalable, Multi-Site DNS Visibility
Enterprise networks are distributed by design. DNS monitoring must follow that distribution.
FlowPro sensors are deployed at individual sites and collect DNS telemetry locally. Enriched data is forwarded to Scrutinizer for centralized analysis and long-term retention, providing a unified view of DNS behavior across the organization.
This distributed collection model supports branch offices, data centers, and cloud environments without requiring architectural redesign or traffic backhauling. Each sensor operates independently at the edge while contributing to a centralized intelligence layer, allowing security and network teams to monitor DNS activity across all locations from a single operational view. This approach maintains performance at the site level while ensuring consistent visibility, correlation, and policy enforcement across the enterprise.
The DNS analytics and threat detection tool supports:
- Centralized visibility across regions and data centers
- Consistent analytics across hybrid environments
- Reduced blind spots across multi-site infrastructures
This makes it suitable for complex industry environments that demand consistent security posture and operational discipline.
FlowPro supports deployment in segmented network zones and regulated environments. DNS data can be collected locally while intelligence is centralized. This allows organizations to maintain segmentation controls without sacrificing visibility or investigative capability.
Protect Your Network with Plixer’s DNS Analytics Solution
FlowPro and Scrutinizer provide an enterprise-ready DNS analytics and threat detection tool that delivers real-time visibility into DNS behavior, correlates that activity with network traffic, and supports precise, defensible investigations. By turning DNS telemetry into operational intelligence, security teams gain clearer insight into suspicious activity and stronger control over how threats are identified and validated.
See FlowPro in action by scheduling a demo and exploring how it integrates with your existing security and monitoring architecture through Scrutinizer. Evaluate how DNS-driven intelligence can strengthen detection capabilities and streamline investigation workflows.
Request a Demo