One Platform,
One operational Truth
Correlate network, application, and security data in a single, unified view.
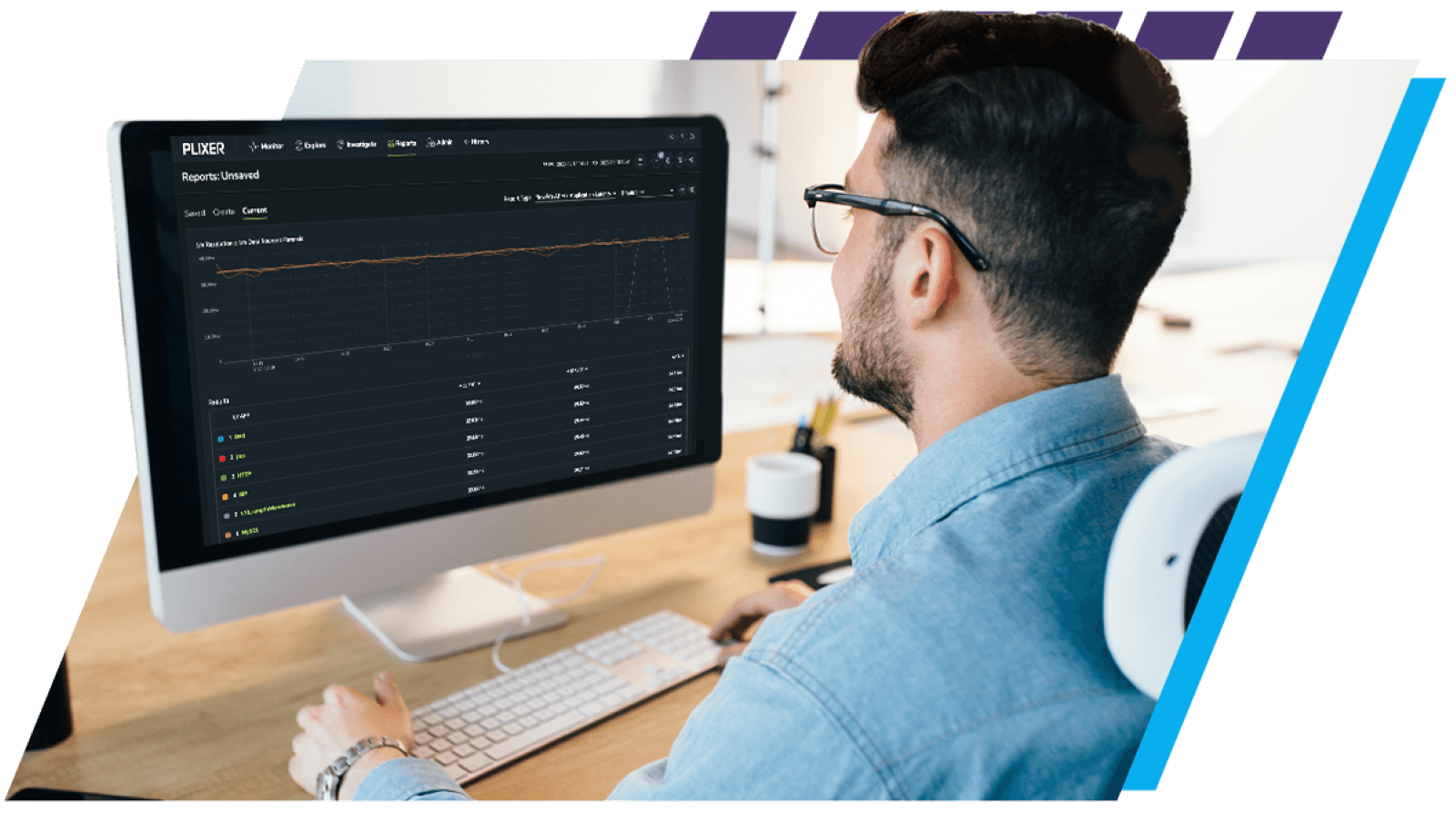
Find and
Fix Faster
Trace latency and packet loss to the slow segment in one view.
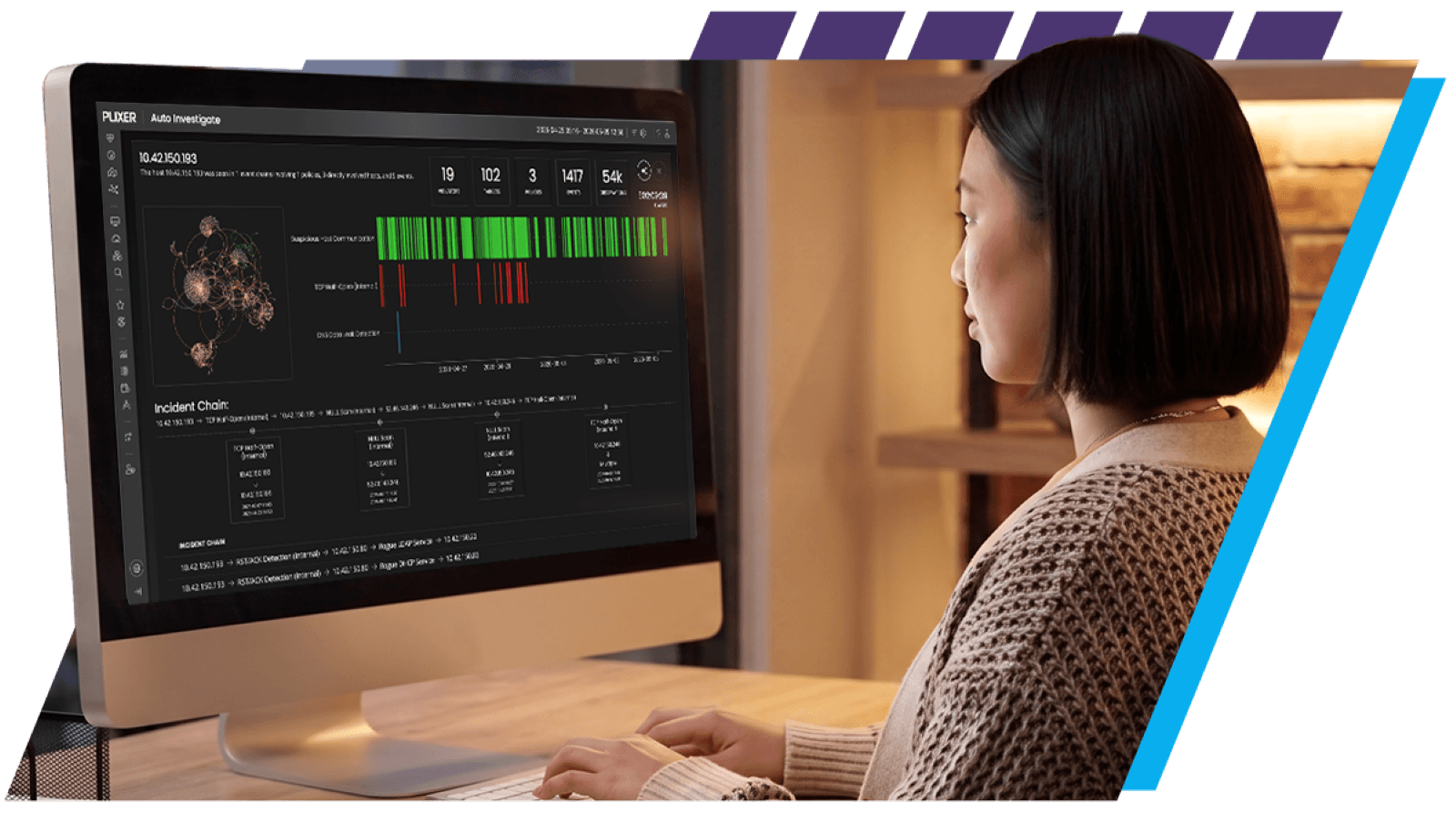
Detect and
Stop Threats
AI-driven detection exposes command and control traffic and lateral movement instantly.
AI That Speeds Resolution
Ask questions in plain language and get the right report with next steps.
Network Telemetry Distribution
Policy-based UDP replication delivers complete visibility to every tool that needs it.
Unified Observability at Enterprise Scale
Plixer One Enterprise is a comprehensive observability platform that correlates network, application, and security telemetry across on-prem, cloud, and zero-trust environments, turning complex traffic, device behavior, and user activity into shared intelligence for NetOps and SecOps teams. This unified observability view enables organizations to move beyond traditional monitoring approaches.
without probes or agents, giving teams full stack visibility into traffic, devices, and distributed applications.
that surface anomalies instantly and highlight performance issues before they escalate.
that shows devices, users, and services, using flow based tracing to follow activity across the entire data path.
replacing multiple tools with a single platform that speeds investigation and reduces operational load.
Plixer In Action
How we are helping Organizations Elevate Network Management and Security Operations