Navigating the Rising Tide of Stealth Cyber Threats: A 2024 Perspective
As we navigate through 2024, the cybersecurity landscape is increasingly dominated by stealth and sophistication. The recent CrowdStrike Global
Read MoreCategory: Security Operations
As we navigate through 2024, the cybersecurity landscape is increasingly dominated by stealth and sophistication. The recent CrowdStrike Global
Read More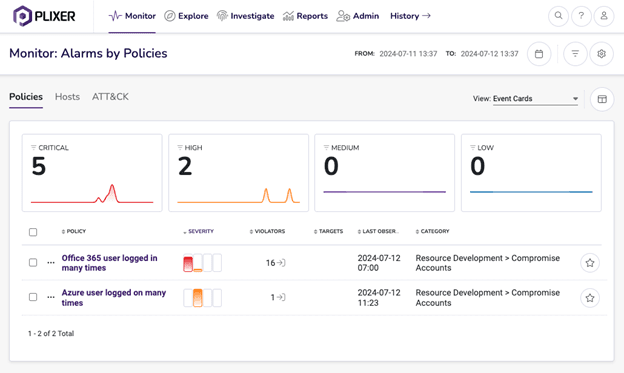
User and Entity Behavior Analytics (UEBA) provides the critical insights needed to identify these hidden dangers by monitoring behavioral
Read More
Author: Ryan Mellmer, Plixer Software Engineer The world is currently in an AI (Artificial Intelligence) revolution. AI is everywhere
Read More
Author: Stephanie Kille, Customer Success Manager, Plixer Recent years have seen a disturbing trend of healthcare data breaches, with
Read More
The digital landscape can sometimes seem a bit like a dense forest after dark, with new and unseen threats
Read More
Any security analyst will tell you that the most challenging part of the job is knowing what to respond
Read More
Data security is a critical aspect of any organization’s IT infrastructure. With the explosion of cyber threats, it has
Read More
How prepared for an attack are you? The most recent Microsoft Defence Report found volume of password attacks has
Read More
XDR stands for eXtended Detection and Response. What it is depends on who is explaining it. XDR evolved very
Read More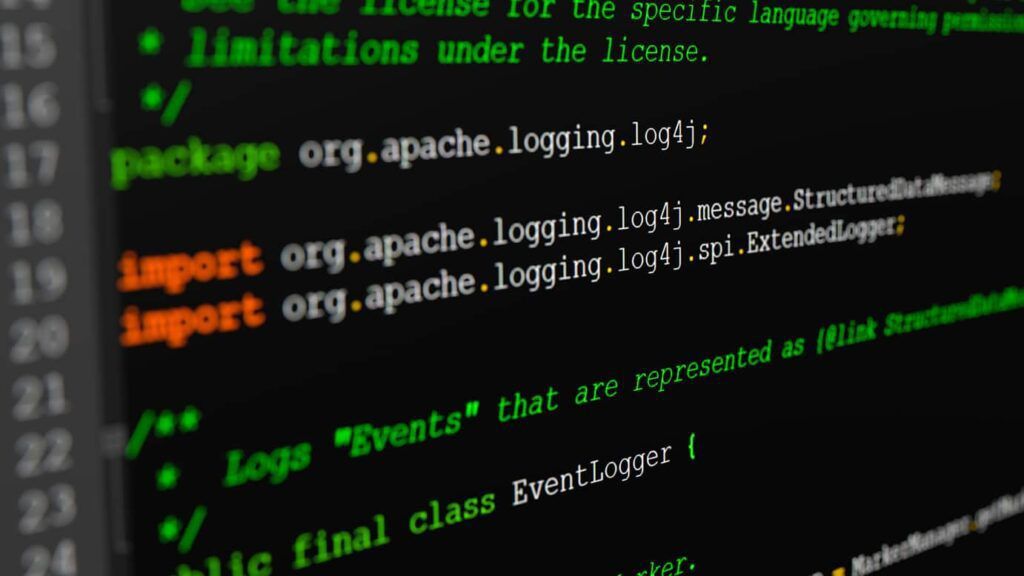
Earlier this month, a vulnerability in the Apache Log4j logging framework was disclosed. The zero-day vulnerability was published by
Read More