It can happen to anyone, even the most seasoned of network security personnel. You can be searching for something on Google, see a seemingly innocent link that looks like exactly what you’re looking for, and click it. Next thing you know, your computer screen is flashing with a message that says your computer is infected and you need to call the following number ASAP. If this does happen in your office, don’t worry: we can help.
Sneaky links
Sadly, this sort of thing did happen to me. A couple of months ago, my husband and I were thinking of making some home repairs. While chatting, he asked me to wait one second while he googled what we were looking for. I heard him type, click, then another click, then a gasp as he stood up and ripped the ethernet cable out of his desktop. We got lucky; he was able to close the page and then run a couple virus scans, which came back clean.

What happened? Well, when his search returned results, he clicked on the first link. Curious, I made the same search and the same exact link came up. I didn’t click it, but I did hover over it to see where the link went. The link said it went to the correct website; however, when I hovered over the link, it said it led to a page for a kiddie pool, which I was not searching for at all. So what happened here? I’m pretty sure chain hardware stores are not routing their pages to a ransomware site on purpose. If you want a little more information on a similar situation, you can follow this trustworthy link.
How Plixer Scrutinizer can help find malicious links
It’s going to happen. You’ll have employees that shop while on the clock using company computers and/or company internet. This is a fact of life; another is that there’s a good chance someone looking for great deals on the latest phones is going to click one wrong link and end up in the same situation I did.
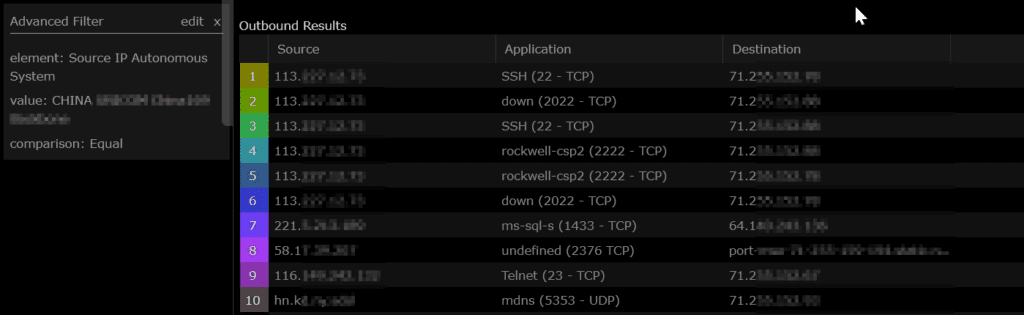
If you’d like to avoid being “that guy” in the office, you can take a look at these tips for avoiding ransomware. The good news is, Plixer Scrutinizer can help you track down bad links and IPs in a couple different ways. Depending on what type of exports your router, switch, or firewall are sending to Scrutinizer, it can show you host-to-host traffic with next-hop information, reverse second-level domain names, and even FQDN reports. What about networks that use NATing? Yup, we can look at all NAT details too, including source IP, NAT source IP, NAT destination, and destination, putting together the whole chain. My favorite report, though, is the autonomous system names. With it, it’s incredibly easy to see at a glance where your traffic is going to and coming from, reducing Mean Time To Know and reaction time. By filtering on a suspicious AS name, you can see which hosts have been reaching out to that destination, as you can see in the screenshot above.


