Network Detection and Response (NDR): What does it mean?
What is NDR? This blog will focus on the hottest 3-letter acronym of 2020 & 2021—NDR. Network Detection and
Read MoreCategory: Security Operations
What is NDR? This blog will focus on the hottest 3-letter acronym of 2020 & 2021—NDR. Network Detection and
Read More
Gartner just posted their worldwide spending forecast report for the first quarter of 2021 and it looks positive. Clearly,
Read MoreThe need to detect and mitigate denial-of-service attacks is nothing new to network and security administrators. DoS attacks on
Read More
Ping is one of those protocols that no one thinks about until it isn’t working and you’re trying to
Read More
I don’t know about you, but it seems like there’s news of some big data breach every other month.
Read More
I think I can safely assume that everyone knows the cautionary tale of the boy who cried wolf. If
Read More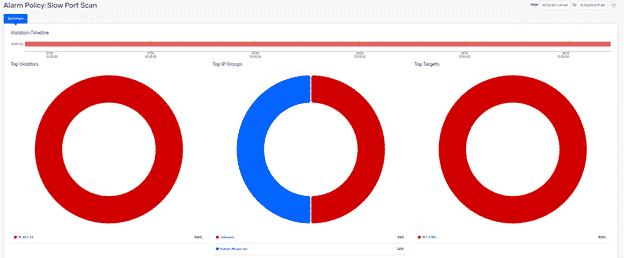
As enterprises adjust to the new normal and remote work, they are bracing for potential attacks resulting from employee
Read More
Even though most of us have looked at a calendar recently and thought, “I could have sworn we were
Read More
I was recently able to explore the Splunk software development kit with a customer. This helped me to implement
Read More
A few years ago, we added a behavioral algorithm to Plixer Scrutinizer that looked at all the flow data
Read More