
How to detect suspicious ICMP traffic
A few years ago, we added a behavioral algorithm to Plixer Scrutinizer that looked at all the flow data
Read MoreInsights, updates, and technical deep dives from our team

A few years ago, we added a behavioral algorithm to Plixer Scrutinizer that looked at all the flow data
Read More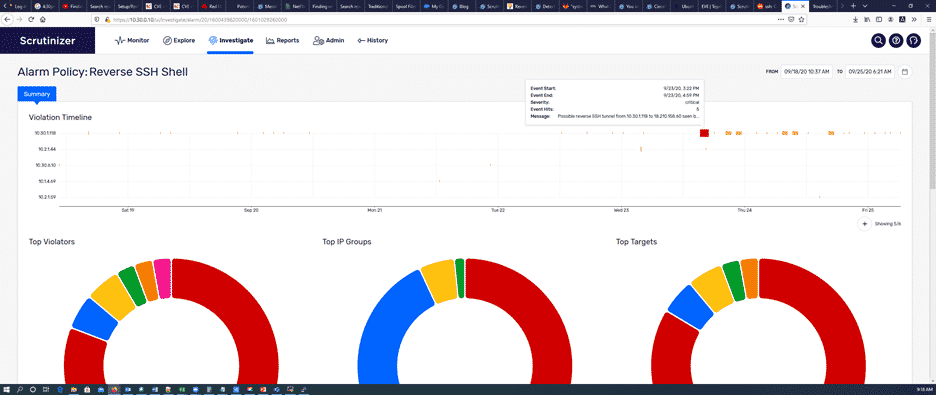
Today we are going to talk about Plixer’s new Flow Analytics algorithm, Reverse SSH Shell, which has been included
Read More
What is STIX/TAXII? STIX stands for Structured Threat Information Expression, which is an open-source language and serialization format used
Read More
The purpose of this blog is to de-mystify the hype around machine learning (ML) by exploring three topics: What
Read More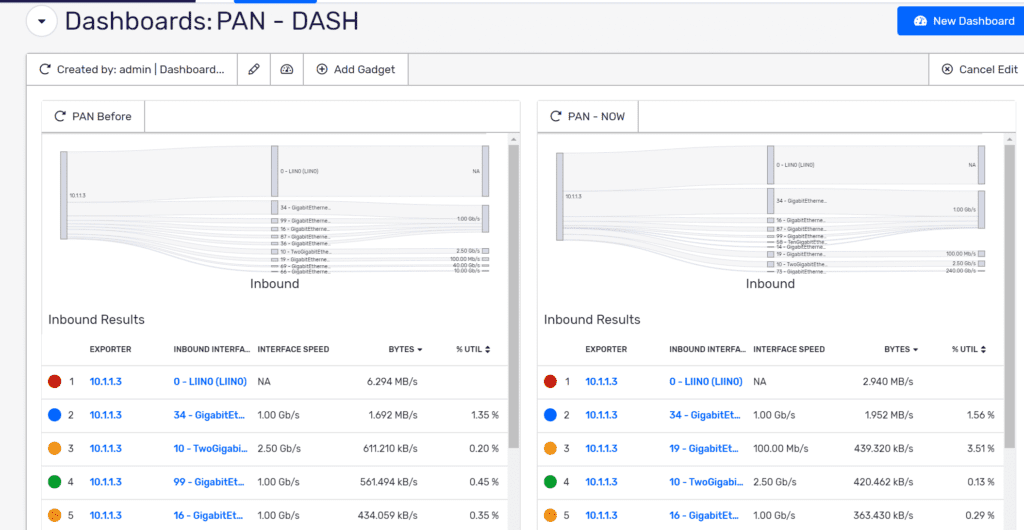
When this pandemic started and nearly the entire workforce went remote, our focus was to maintain the quality of
Read More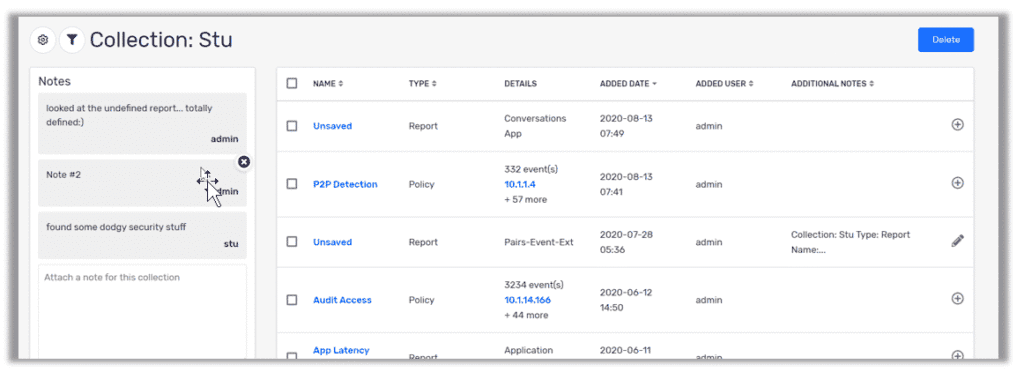
I can’t tell you how many calls I’ve been on where the NetOps and SecOps teams really don’t know
Read More
Many ISPs filter bogon connections because bogon IP addresses have no legitimate use. If you find a bogon or
Read MoreOne year ago, we announced our new vision. That is, we believe that SecOps and NetOps provide value for
Read More
A common tactic for bad actors to get a foothold into the network is to leverage IP spoofing to
Read More
Competition generally ends up being good for the consumer. It keeps prices down and forces innovation as vendors compete
Read More