Why Downtime Prevention Starts with Proactive Monitoring
Downtime has become one of the most expensive and disruptive challenges in IT operations. Whether it’s a service interruption,
Read MoreCategory: Network Security
Downtime has become one of the most expensive and disruptive challenges in IT operations. Whether it’s a service interruption,
Read More
When an incident hits, you need to know what happened, how it spread, and which systems were touched. That’s
Read More
The way organizations grow today looks very different from a decade ago. Expansion now requires building digital ecosystems that
Read More
Endpoint agents have long been treated as a necessary trade-off. They offer local insight, but they also add risk:
Read More
Flow visibility may be easy to forever leave on the back burner, but its absence is one of the
Read More
In any organization, the network is both the backbone of operations and the first witness to incidents. Every service
Read More
Healthcare organizations face unique challenges that demand both exceptional network performance and ironclad security. From ensuring patient data remains
Read More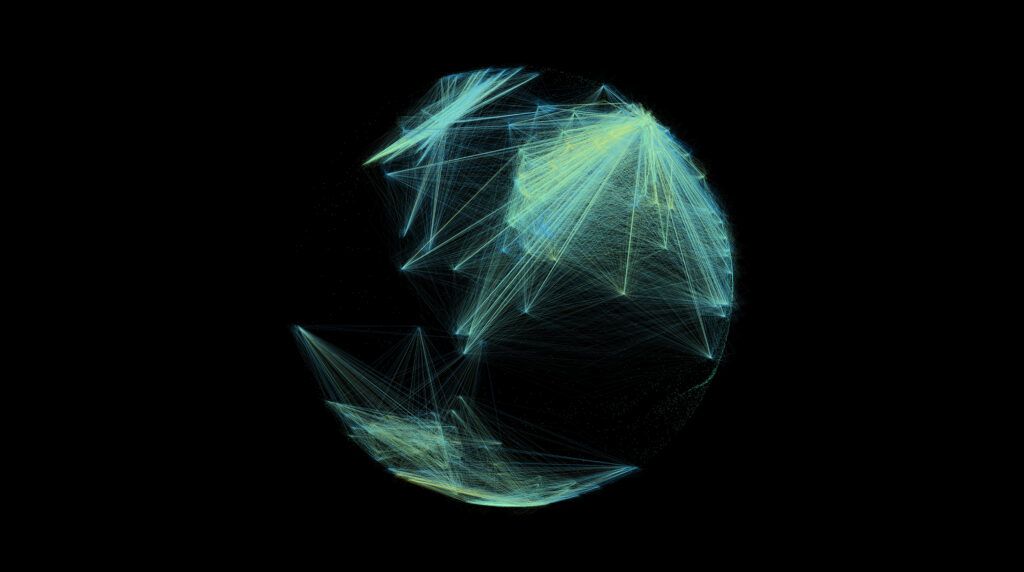
The modern enterprise network has evolved far beyond the predictable, perimeter-based architectures of the past. What once existed as
Read More
University networks face a fundamental monitoring challenge that traditional tools struggle to address effectively. Campus environments combine massive scale,
Read More
Financial services organizations face an unprecedented convergence of challenges in 2025, including an increased risk of ransomware attacks and
Read More