
What is Zero Trust? Principles, Implementation, and Challenges
As traditional perimeter-based defenses prove inadequate against today’s cyber threats, Zero Trust offers a flexible and comprehensive model grounded in the principle of “never...

As traditional perimeter-based defenses prove inadequate against today’s cyber threats, Zero Trust offers a flexible and comprehensive model grounded in the principle of “never...

Security debt is emerging as a critical concern for IT and security teams. As businesses rapidly adopt new technologies, many carry forward legacy systems,...

Healthcare data security is not just an IT concern, but a fundamental pillar of patient care and organizational survival. From electronic health records (EHRs)...
Unlike accidental data leaks caused by human error or misconfigured systems, data exfiltration is a deliberate and malicious act. It involves the unauthorized transfer...

As more businesses have migrated to the cloud, the question of how to protect digital assets in these dynamic, distributed environments has become critical....

For security teams, early detection is the difference between a minor incident and a full-scale breach. That’s where Indicators of Compromise (IOCs) come into...
Insider threat detection has become one of the most critical aspects of modern cybersecurity. Unlike external attacks, which originate from outside an organization, insider threats...
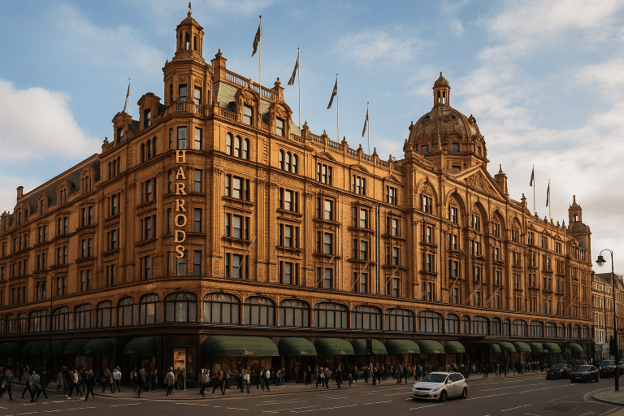
Author: Adam Boeckmann | May 2025 Recent attacks on major UK retailers, including Harrods, M&S, and Co-op, have highlighted a critical reality: even iconic brands...

Author: Adam Boeckmann | April 2025 As financial institutions across the EU prepare to meet the requirements of the Digital Operational Resilience Act (DORA), one...

As attackers grow more sophisticated and persistent, organizations are shifting from reactive defense to proactive strategy. That’s where cyber threat intelligence (CTI) comes in. ...