
How To Investigate Encrypted Traffic Without Decrypting It
Most malicious traffic is encrypted, and in real environments, you usually don’t have the keys to inspect it. You can still investigate encrypted traffic effectively by ...
Read MoreInsights, updates, and technical deep dives from our team

Most malicious traffic is encrypted, and in real environments, you usually don’t have the keys to inspect it. You can still investigate encrypted traffic effectively by ...
Read More

Lateral movement is rarely loud. Once an attacker gains an initial foothold, the next phase often blends into normal
Read More
SD-WAN was supposed to simplify the network. In many organizations, it did the opposite. Abstracted tunnels, dynamic path selection,
Read More
University networks face a fundamental monitoring challenge that traditional tools struggle to address effectively. Campus environments combine massive scale,
Read More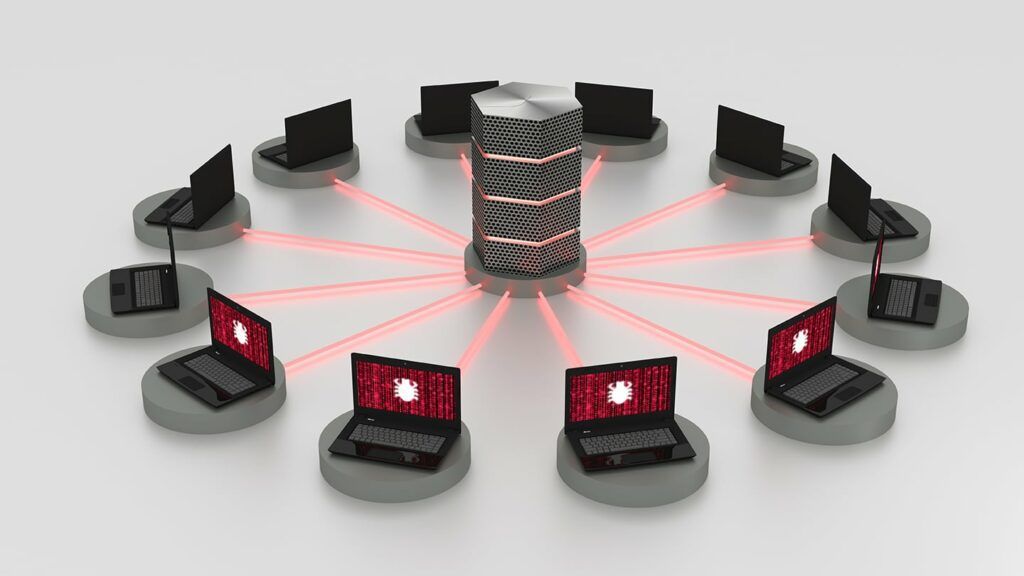
As more and more devices are added to the internet, a larger swath of insecurity comes with them. Botnets
Read More
I spent a lot of time talking to customers at RSA 2019 and a message that resonated with a
Read MoreIn this line of work I find myself talking with network professionals daily. With this constant exposure to a
Read MoreNetFlow is widely regarded as an ideal technology for acquiring summarized details on network traffic; as a result one
Read MoreIn this blog, I will be continuing Part 1 of the “What is Flow Analytics™?” Series. In this blog I
Read MoreOftentimes, when I’m running around the country setting up Flow Analytics, I don’t see Null Scans pop up. However,
Read More