Last week, Joanne started a series of blogs aimed at providing an overview of some NetFlow basics. I am going to continue this series and take a look at what can be found in the NetFlow Packet header.
Built by a device (for example, a router) with NetFlow services enabled, the NetFlow export packet is addressed to a NetFlow collector. The collector processes the packet and stores the information found in the IP flow records.
The NetFlow record format consists of a packet header followed by at least one or more template or data FlowSets.
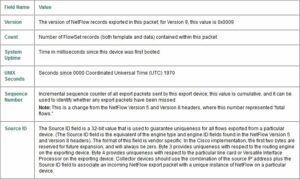
The Packet header is the first part of an export packet and provides basic information about the packet. Information included in the packet header is the NetFlow version, number of records contained within the packet, or the length of the flow records, a sequence number, enabling lost packets to be detected, and a date/time stamp.
The following is the packet header layout and field descriptions:

Here is what the packet looks like in Wireshark:
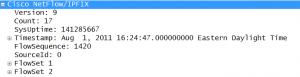
Notice in this case, how we are sending NetFlow version 9, and that we have a flow record count of 17. This is telling us that we have a number of FlowSets that in total have 17 flow data records. Also notice the FlowSequence number. Scrutinizer keeps track of these and will let you know if you are dropping packets or they appear out of sequence.
We will be taking a closer look at the flow sets in the next blog in our NetFlow overview series.
What do you need to get from NetFlow reporting? For the most Advanced NetFlow reporting and Security monitoring solution available, point the NetFlow exports to our award winning NetFlow Collector. Scrutinizer fully understands all of the different vendor exports, and lets you take advantage of all of the latest flow technologies.
Please let us know if we can help you get NetFlow configured in your network.