It’s becoming more and more evident that an effective cyber threat incident response system requires the implementation and fine tuning of a variety of tools like Host Reputation and Domain Reputation. Among the arsenal of tools at your disposal are some that take a fine grained approach to preventing or rooting out the bad, and others that take a broader approach.
Our incident response system contains tools that provide the kind of deep visibility that will ensure your team can determine malware’s origin, find the root cause of infection, and contain the threat before it causes extensive damage. Today I’m going to tell you about two similar but highly specialized tools that offer strong protection against intrusion on your network: Host Reputation and Domain Reputation Flow Analytics.
Host Reputation:
Using NetFlow data, the Host Reputation algorithm compares the hosts your internal devices are communicating with to a list of IPs in the Host Reputation database. The database is updated routinely and provides a comprehensive list of compromised sites known to be the source of malware and Tor nodes used for Command and Control communications by cyber criminals. The Host Reputation algorithm is customizable.
For example, your incident response team may discover in the course of an investigation using other tools at it’s disposal that a certain host or hosts should be added to the list of hosts that will trigger an alarm when communication with them is detected. Adding the hosts to the database constantly being used in comparison checks is simply matter of adding the IP address to a certain text file.
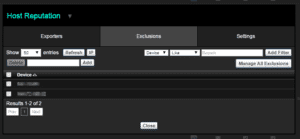
You may need to allow some of your users to have access resources that appear in the database. You can add those users to a Host Reputation Exclusion white list to avoid triggering an alarm for their authorized access to URLs that would trigger an alarm when used by others.
Armed with this detection tool, your incident response team can react quickly when an alarm is triggered, find the user who’s engaging in risky activity and put a stop to the behavior before the whole network is affected.
Domain Reputation:
The latest addition to our suite of Incident Response tools is Domain Reputation. Domain Reputation monitoring is actually performed by FlowPro Defender. When FlowPro Defender detects interaction with a domain in its list of over 400,000 bad domains, it sends the information on to Scrutinizer for further processing. Plixer provides the domain list to FlowPro Defender and updates it every hour. Domain Reputation monitoring is much more accurate than Host Reputation, and results in far less false positivie alarms. By default, any activity involving domains on the list will trigger an alarm.
Domain Reputation can be configured on FlowPro Defender to allow certain applications to access domains in a Trusted Domains list. Once configured, authorized applications will no longer trigger alarms.
Domain Reputation is also customizable, like Host Reputation, to allow users to define a list or series of lists that contain any domains that are not in the domain list maintained by Plixer.
Properly configured and maintained Host Reputation and Domain Reputation tools are essential weapons in the arsenal you create to defend your network. Find out how the integration of these tools in our Incident Response System provides that solution for you.