Navigating the Rising Tide of Stealth Cyber Threats: A 2024 Perspective
As we navigate through 2024, the cybersecurity landscape is increasingly dominated by stealth and sophistication. The recent CrowdStrike Global
Read MoreInsights, updates, and technical deep dives from our team
As we navigate through 2024, the cybersecurity landscape is increasingly dominated by stealth and sophistication. The recent CrowdStrike Global
Read More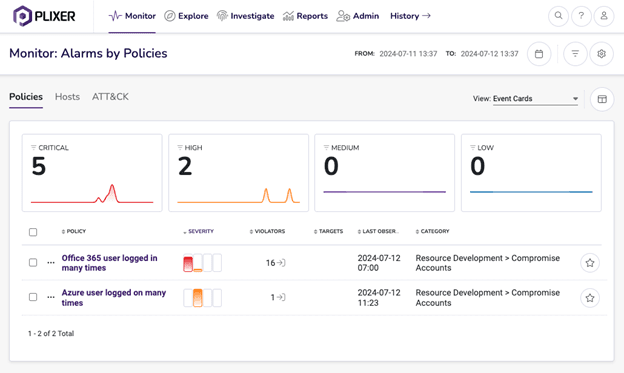
User and Entity Behavior Analytics (UEBA) provides the critical insights needed to identify these hidden dangers by monitoring behavioral
Read More
The big boss had a conference call over the weekend. She sent a message to your boss’s boss, which
Read More
When it comes to filtering network traffic, a scenario that appears simple in nature can be hard to accomplish
Read More
There are times when we adults would be better off thinking like toddlers. More specifically, I want us all
Read MoreSo you are thinking of delving into the world of Linux NetFlow Collectors, but do not quite know where
Read MoreVMware IPFIX support and our IPFIX collector, Scrutinizer, give you visibility into the ‘cloud’. In this blog, I will
Read MoreLet’s talk about UDP scans and how they can be an internet threat. In today’s world, having multiple layers
Read MoreNow more than ever banking Internet security is at the forefront of nearly every CIO, CTO and Director of
Read MoreXirrus IPFIX support provides network admins greater insight into what is going on out at the edge. Understanding which
Read More