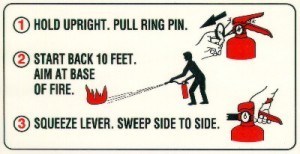
When I was studying at the University, every floor of every dorm had a fire extinguisher. I sort of assumed that the school had learned from history that a fire will likely break out again some day. The red tanks on each floor were a proactive measure in preparation for the seemingly inevitable and I remember the instructions “in case of fire, pull pin and squeeze lever”. Simple – and it implied to me that the school was trying to be prepared.
Those fire extinguishers have some people thinking about malware preparations. What does the company have in place to react to a malware incident? Does the IT team have a document listing the series of steps to be followed depending on the type of event? Most don’t. This of course is a bit concerning considering that most large organizations today feel they are likely already carrying infections internally.
“All organizations should now assume that they are in a state of continuous compromise,” a February report from IT research firm Gartner advised. “Comprehensive protection requires an adaptive protection process integrating predictive, preventive, detective and response capabilities.”
A company’s cyber attack incident response must be timely and in order to react swiftly, several areas must be addressed:
- Assigned personnel: who is responsible for managing the follow up to a discovered breach?
- Documentation: what must be done given the type of incident the security team is faced with?
- Training: do the people tasked with the clean up have the necessary skills to react quickly?
- Fire drills: has the team tested themselves to ensure timely – prudent response times?
- History: does the IT department have a warehouse of log and flow data that can service malware incident response?
The above items, especially the fire drill, are critical measures that will help your team recover from the inevitable security compromise. A breach is going to happen, we must prepare the company. Cisco stated that “More than 90 percent (93.75 percent) of customer networks observed in 2014 have been identified as having traffic going to websites that host malware. Specifically, the networks have been identified as issuing DNS requests for hostnames where the IP address to which the hostname resolves is reported to be associated with the distribution of, or is infected by, Palevo, Zeus, or SpyEye malware.”
You can bet that when a suspicious event is uncovered, the incident response team will want to roll back the clocks and trace the infection to all the other hosts that may also be infected. A good incident response system can provide this capability.