Let’s discuss configuring Plixer’s Replicator. This UDP replicator provides NetFlow duplication and forwarding to multiple collection points. The Appliance doesn’t just stop there. It can also serve as a central staging point for syslogs, SNMP, and other UDP messages. This simplifies your network configuration and reduces the traffic load on your routers and switches. While the Replicator boasts many powerful qualities, command-line verbosity isn’t one of them. So if you’re staring at the command prompt and wondering, “I have a Replicator up and running, now what do I do?” here are some quick examples of configuring your replicator to get the most out of this dynamic tool.
This guide assumes you’ve got the Replicator appliance up and running. If you haven’t reached this point you can start with the README that’s bundled with the replicator. We’ll pick up from the Replicator’s command line interface, logged in as the user ‘replicator’.
NetFlow Duplication: Forwarding from all hosts to multiple Collectors
NetFlow duplication increases data security by providing redundancy. With the UDP Replicator, you can forward NetFlow packets to an unlimited number of collectors. For this example, a humble pair of collectors will do; we’ll start by creating a profile that listens and forwards on port 2055:
profile add fwdallhosts 2055 2055
Commenting is always a good practice. We’ll notate the profile to help out anybody who comes by later. You’ll be grateful if that person is you and you haven’t thought about your configuration for a good, long time:
notate profile fwdallhosts this profile will forward netFlow from all hosts to two collectors
Next we’ll create a policy for the profile that includes all hosts:
policies add 0.0.0.0/0 fwdallhosts include
Now specify the collectors that this profile will forward to. You’ll want to replace A.B.C.D and E.F.G.H with the IP addresses of your collectors. Simply repeat this command for as many collectors you’d like to forward your NetFlow data to:
collector add A.B.C.D fwdallhosts
collector add E.F.G.H fwdallhosts
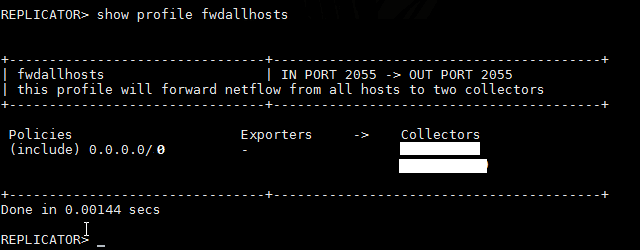
All that’s left is to check our work:
Show profile fwdallhosts
If our syntax was correct we should see something like this:

Forwarding SNMP traps from a single host to two collectors
Akin to network simplification with syslog forwarding, the Replicator provides a great way to consolidate SNMP. This profile will be very similar to the one we just created for syslogs.
Create the profile. This one will listen on port 162. By now you should see a trend in the naming scheme:
profile add fwdsnmp 162 2055
Notate it. Trust, me; you’ll be glad you did:
notate profile fwdsnmp this profile will forward snmp traps to two collectors
Add Collectors to the profile:
collector add A.B.C.D fwdsnmp collector add A.B.C.D fwdsnmp
Add the exporters you expect to receive SNMP messages from:
exporter add A.B.C.D fwdsnmp
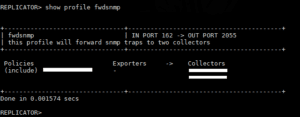
Confirm our configuration:
Show profile fwdsnmp
Forwarding the UDP Replicator alerts to a Scrutinizer server
The previous examples addressed messages originating from other hosts. What about alerts and notifications from our UDP Replicator? Fortunately, this is handled quite efficiently within the “settings” command.
The Replicator’s primary setting for handling alert messages is notificationsent. This setting designates an IP address that the UDP Replicator will forward alerts and notification syslogs to. The syntax is fairly straightforward:
setting set notificationsent A.B.C.D:2055
Now that we have the UDP Replicator configured to forward alarms, let’s take a look at some of the specific alarms we can configure.
flowStopAlert
This setting establishes how many minutes an incoming stream has stopped or a collector is unreachable before the Replicator considers the device down and sends an alert. If you would like to set this to five minutes, the command would be:
Setting set flowStopAlert 5
highCPUThreshold
As the name clearly implies, this alert is triggered when the Replicator’s CPU utilization surpasses the designated threshold. Here’s how to set it to 90%:
Setting set highCPUThreshold 90
pingCollectors & noRepWhenDown
The Replicator’s Deterministic Packet Forwarding feature detects when destination hosts are offline and stops forwarding traffic to them. Enabled by default, the Replicator routinely pings your declared collectors for availability. If “noRepWhenDown” is enabled, the UDP Replicator will stop replicating data to devices it cannot ping. Configuring either of these two settings is easy:
Enabling:
setting set pingCollectors 1 setting set noRepWhenDown 1
Disabling:
setting set pingCollectors 0 setting set noRepWhenDown 0
metricsSent
Not an alarm per se, this will export Replicator statistics as IPFIX data to the IP and port specified:
setting set metricsSent A.B.C.D:2055
Go forth and Replicate!
By now you should see that the Plixer UDP Replicator is more than just a simple Netflow duplication device. Properly configured, the Replicator can become a critical component of your network. From serving as a central data collection point, consolidating system logs, to providing a clearer view of what’s going on. Paired with the Plixer Core Platform, the Replicator gives you unsurpassed oversight and control of your NetFlow data and network status.