Today, many IDS, IPS, and IT Security Forensics vendors purport that most threats are best combated using their Signature-based solutions. Well ‘best’ may be only a small margin of improvement over other threat detection methods. Clearly, the IT Security Threat landscape is expanding and becoming more complex – polymorphic. Although the IDS and IPS do a great job with their signature match strategy, the best approach to IT Security has always been a layered approach.
Network Behavior Analysis
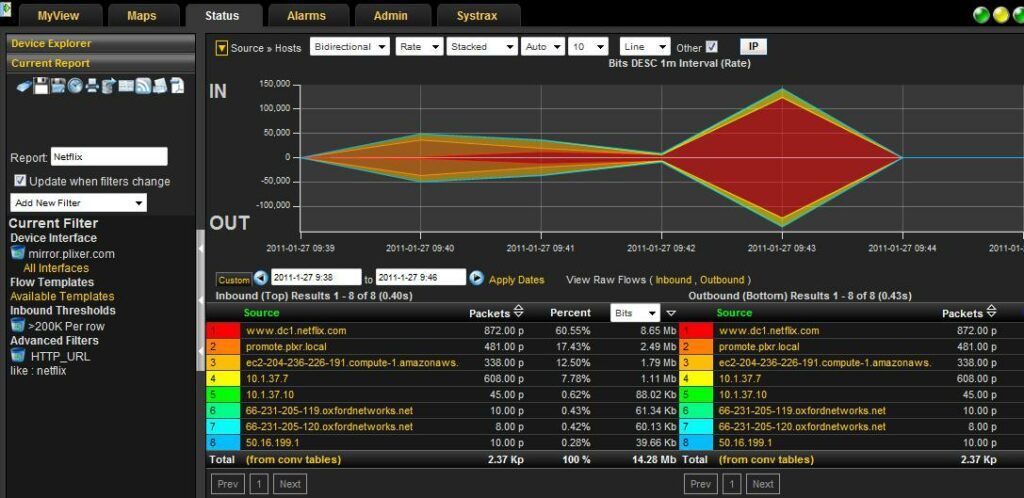
Using flow technologies to monitor communication behaviors and even maintaining baselines is becoming more relevant. When the signatures in the IDS/IPS fail to catch malware, NetFlow and IPFIX can sometimes recognize enough odd behaviors using IT Security Forensics to identify an infection.

“The IDS/IPS is like a blood test, they don’t detect all sicknesses. Using flow data, we can observe symptoms: sore throat, runny nose, chest congestion, itchy eyes, etc. Those are the behaviors of a common cold virus and in a sense, behavior monitoring is what we do with NetFlow and IPFIX. ” Scott Brown – Director of Sales at Plixer
“I’m not saying an IDS/IPS don’t look at behaviors as some do but, their focus is signatures. By using flow data, we can perform IT Security Forensics using behavior monitoring on every router and switch in the entire network (I.e. not just the Internet connection).”
IT Security Forensics with NetFlow
As a result, more is being done with NetFlow and IPFIX and to some extent sFlow. Consider all of the areas where true flow technologies (which sFlow is not) can provide tremendous value:
- Forensic filtering and reporting of nearly any type of traffic related issue:
- Application performance monitoring
- Network congestion
- Malware investigation
- Audits and Compliance (PCI-DSS, HIPAA, GLBA, SOX, DMCA) – storing history
- Denial of Service (DoS and DDoS)
- Smart phone traffic (BYOD)
- Cloud security and performance reporting
- Checking Host Reputation against DNSBLs, which help to identify machines involved with a Botnet or Spam
NetFlow Monitors Traffic Patterns
Signatures need constant updates whereas behavior monitoring is much less dynamic. Since 2006, Plixer has been working with NetFlow to provide IT Security Forensics. Flow Analytics was introduced in 2009 which is used to identify odd communication behaviors. It includes dozens of algorithms that look for the basics such as SYN/FIN violations, network scans, peer to peer (P2P) traffic, odd flow ratios, etc. but, we also include the ability to create custom monitors that are unique to the customers’ business environment. Even baselines will be included this year.
By using flow technologies you gain the ability to setup custom report thresholds based on any filter combination. As a result, you will be alerted to a network issue before the calls start flooding the support center. Ultimately, this results in a lower Mean Time To Know (MTTK).
Next Generation Flow Collecton
Using NetFlow for IT Security Forensics is nothing new. In a previous blog I pointed out how Cisco has bolstered the value of NetFlow, calling it the ‘primary network anomaly detection technology’. Should your organization decide to take another look at your flow collection solution, be aware that Next Generation flow collectors make use of NetFlow and IPFIX for more than just compliance and application performance issues. In most cases, the flow collection appliance is the first server security teams seek out when they need to investigate a threat. This is true regardless of whether it was the IDS, IPS, antivirus or Flow Analytics that discovered the suspicious traffic.