Businesses with IT Teams managing tens of thousands of IP addresses often find it more difficult to track down IP addresses and for this reason, they would rather work with a username. Identity Aware NetFlow ties the two together. In this post, lets take an example of tracking down the root cause of a network security issue or detected threat.
Network Behavior Analysis
Our network behavior analysis solution using NetFlow can identify zero-day attacks, data leakage, Command and Control (C&C) bots, Advanced Persistent Threats (APT) and other types of malware. What if the system only offers up the IP address when a nefarious event occurs, how easy is this to track down? Would it be better if presented with a username as well? Most IT administrators would agree that it would in fact help.
Identity Aware NetFlow
This username or identity-aware NetFlow is the same information that has proved useful in BYOD Traffic Monitoring. It allows seasoned professionals to identify all of the users responsible for a performance problem or involved with spreading an infection. Access to all of the contextual information surrounding suspicious hosts and network behaviors quickens the forensic investigation process empowering IT to quickly mitigate problems.
According to the Cisco Connected World Technology Report regarding security-related issues in the workplace, seven out of ten employees admitted to knowingly breaking IT policies on a regular basis, and three of five believe they are not responsible for protecting corporate information and devices.
HIPAA and PCI Compliance
Another benefit to Identity Aware NetFlow is the ability to track users in DHCP environments where IP addresses can change frequently. Usernames don’t typically change that often. For all of these reasons, Identity-Aware NetFlow improves accountability for not only IT but for Human Resources should reports need to be run depicting an entire history of network use by a username. It is no surprise that auditing efforts are also improved by NetFlow and IPFIX when compliance becomes a factor. NetFlow supports the businesses need to be HIPPA and PCI compliant.
Cisco ASA NSEL Exports Username
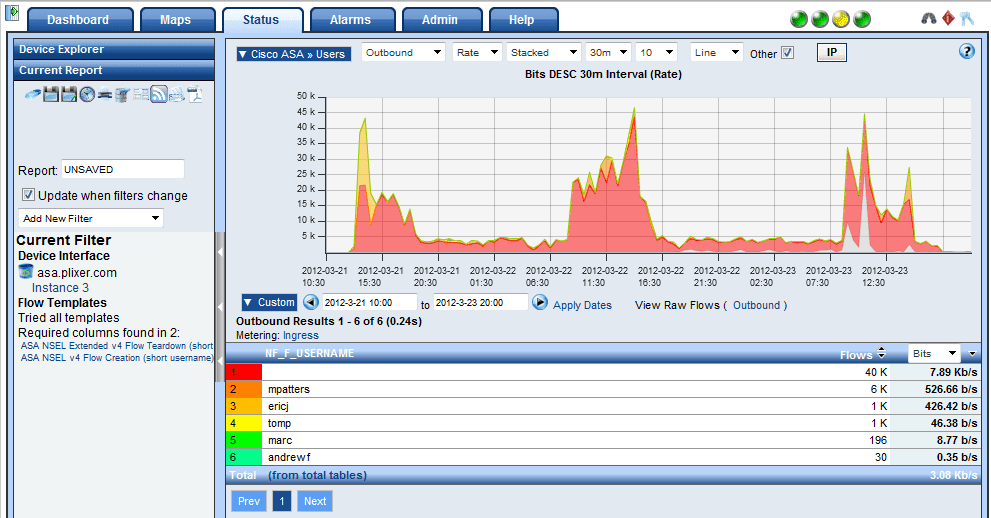
The first place we found Identity Aware NetFlow as from the Cisco ASA NSEL NetFlow exports as shown in the following figure.
Usernames in NetFlow exports can also be found in the SonicWALL IPFIX exports and from the Palo Alto NetFlow export. When username details are not available in the flows, we can extract them from Cisco ISE, Enterasys Mobile IAM or other means. Our NetFlow and Network Security Solution delivers deeper visibility into network misuse whether the problem is malicious or a specific policy violation. We offer award winning advanced flow reporting and threat detection on all firewalls supporting NetFlow or IPFIX.