Recently, there has been an increase in distributed denial-of-service (DDoS) attacks that involve the use of compromised IoT devices like IP cameras, and it is extremely common today for organizations and consumers to purchase IoT devices. So how can organizations reduce the IoT threat surface that these devices bring, and how can they see what these devices are doing?
Reduce the number of IoT devices on your network
While this may sound like an obvious solution, it’s likely not something you’ve considered given the availability of these devices in the market. But have you considered alternatives, or have you considered abandoning the purchase all together? Sure, that IP camera setup is extremely easy and doesn’t require you to drill holes, but connecting it to your corporate Wi-Fi may not make the most sense. Many hardwired versions of popular IoT devices are available and can provide similar functionality without the added risk associated with them.
Isolate the devices
 Okay, so you must have that IoT coffee bar with built-in voice control to create that perfect cappuccino in the morning. But you don’t have to add it to the corporate network to use its internet-enabled features. When you have a device that requires internet connectivity, deploy the device on a guest network instead of the main, corporate network. This setup will allow the device to connect to the internet for updates and to retrieve those updated macchiato recipes you so desperately desire, but will keep the devices from connecting to business-critical applications and wreaking havoc on your corporate assets. We know you must have your iced quad upside-down caramel macchiato with light ice, but let’s make that possible while reducing the threat surface.
Okay, so you must have that IoT coffee bar with built-in voice control to create that perfect cappuccino in the morning. But you don’t have to add it to the corporate network to use its internet-enabled features. When you have a device that requires internet connectivity, deploy the device on a guest network instead of the main, corporate network. This setup will allow the device to connect to the internet for updates and to retrieve those updated macchiato recipes you so desperately desire, but will keep the devices from connecting to business-critical applications and wreaking havoc on your corporate assets. We know you must have your iced quad upside-down caramel macchiato with light ice, but let’s make that possible while reducing the threat surface.
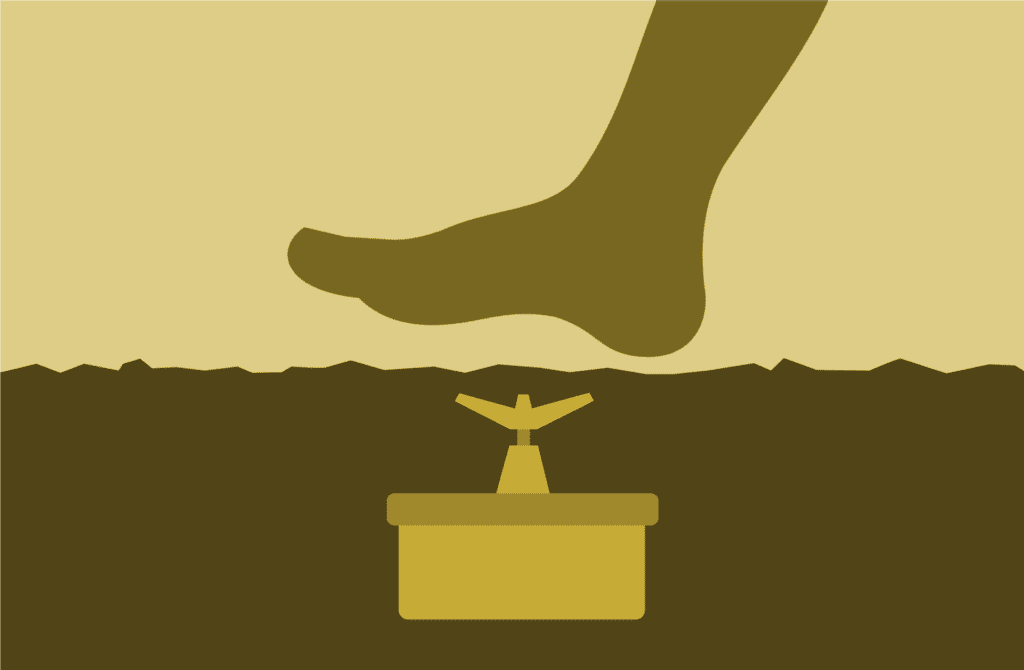
Deploy devices with least privileges
So your coffee bar might be something you can get away with putting on a separate, isolated network, but some devices might require connecting to an application or server on the main network. Fret not; it is still possible to deploy the IoT device on the corporate network without adding too much risk (risk is always possible when deploying any device).
When deploying IoT devices on the main network, they should always be deployed with a least-privilege approach. This means that you will deploy the device on the network, but the device will be locked down from communicating to everything that isn’t absolutely required.
Imagine you are deploying a new IP camera system that connects to the internet to provide DVR-like functionality. This new system will likely have a central storage server (either on the local network or online) where the individual cameras connect. In this setup, the IoT system is very limited in its requirements. Specifically, the individual cameras only need to communicate to the local, internal server for storing the video, or a limited set of connections to the internet (a range of IP addresses or hostnames where the internet server is located). Because of this, you can fairly easily limit the communications from the cameras by creating an ACL for these IP cameras and allow connections to the limited number of devices required to record and store the necessary video effectively.
Monitor IoT devices for anomalous behavior
If you are going to deploy IoT devices on your network, you need to monitor the traffic that these devices are generating. While ACLs are an important step in a multi-layered approach to network security, you must have a way to detect and alert on breaches to these policies. When the IP camera starts to communicate to the mail server or attempts to access your financial documents, a red flag should immediately be raised because, after all, these devices are purpose-built and have no viable reason to communicate with these servers or applications.
By having the insight on these IoT devices, you can reduce your IoT threat surface while still maintaining the convenience and improved performance that these devices provide.
If you would like to learn more about monitoring IoT devices on your network and leveraging network traffic analytics to see when they are communicating with device unrelated to their function, download Scrutinizer today; our team will help you get set up.