Experience Total Network Observability & Defense
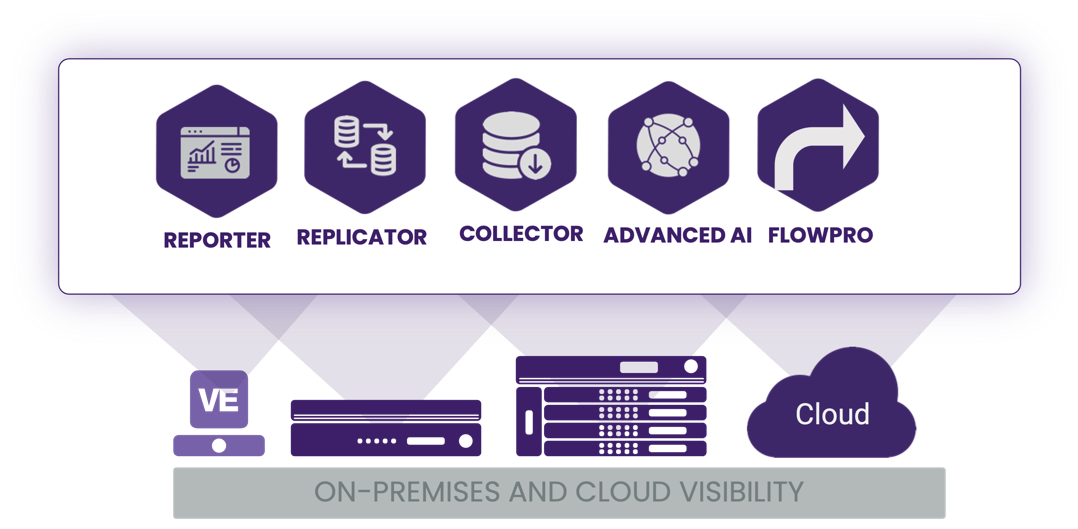
Plixer One Platform
Ensuring the Power of the Network starts with visibility and control
See More.
- Ingest data from every critical network component and path in the datacenter, hybrid cloud, and global eco-system
- Visualize the entirety of network activity in real-time without blind spots
Know more.
- Automatically correlate flow data and leverage advanced analytic and AI for richer context, insights, and understanding
- Ensure your team can answer to what is happening in the network.
Do More.
- Plan, update and defend the network easily and effectively improve operations
- Optimize existing IDS/IPS, DDoS defense, NDR, XDR, NFW, and SIEM to strengthen defenses
Harness network data and observe network traffic everywhere in your distributed data center environment and the cloud

Experience Total Network Observability and Defense
Plixer One Platform uniquely elevates enterprise network visibility, leveraging NetFlow/IPFIX data that exists at every critical points throughout your IT environment. Discover the power of full-scale network observability with defensive controls that eliminate blind spots, minimize performance risk, and identify and respond to concerning events and traffic patterns fast.
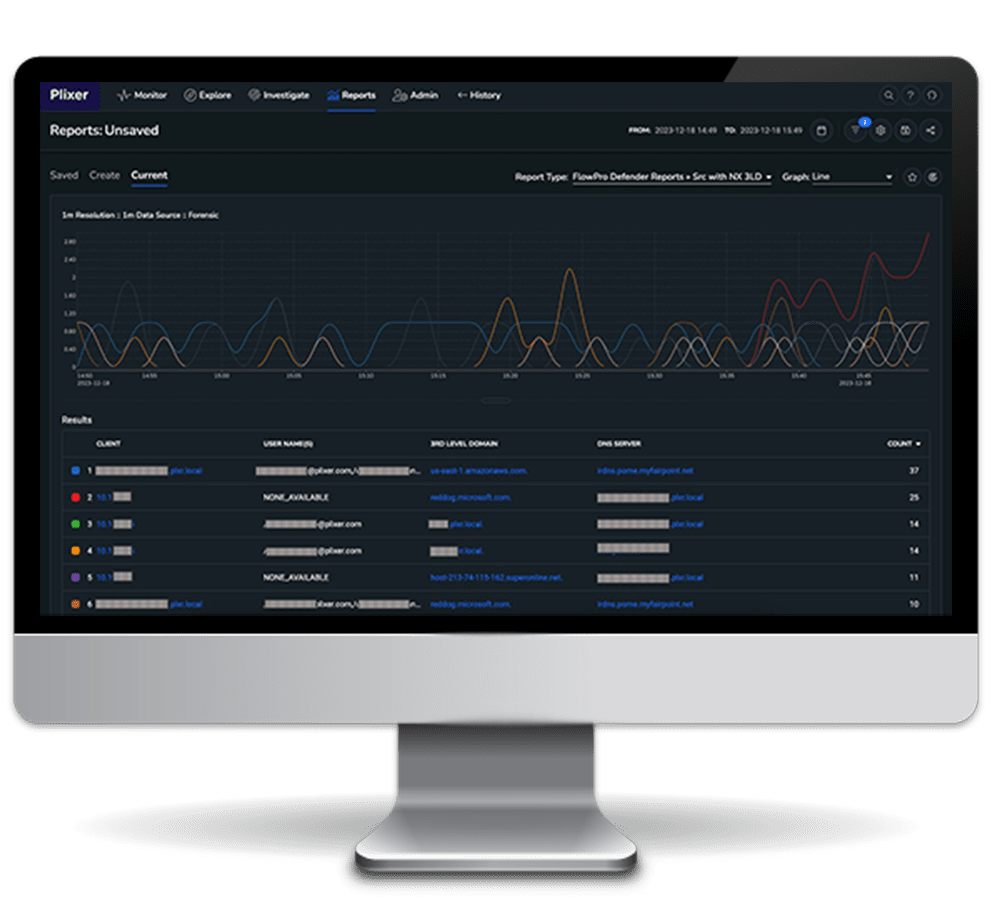
Reporter
Correlates, analyzes and visualizes collected network data for a full view of the state of the distributed evironment, and with forensic and contextual insight, for effective research, hunting, performance monitoring, and rootcause analysis.
Replicator
Channels ingested flows and metadata with speed, duplicating, and forwarding data for storage, management and analysis without complexity.
Collector
Collects and stores an unlimited amount of formatted historical network data from across the ecosystem.
Flow pro
Enables deep packet inspection for DNS monitoring, IDS and layer 7 defense more effeceintly.
Advanced AI
Employs ML, predictive modeling and deep learning to extract intrinsic network knowledge.
Address the gaps in your visibility fabric with Plixer One.
Uncover Network Blind Spots with Plixer One
According to Computer Weekly, 84% of network professionals struggle with blind spots and are challenged at leveraging data amassed in the network as the ecosystem expands beyond the visibility fabric, especially while teams operate in silos. What are you not monitoring?
Learn how to eliminate blind spotsNetwork Performance & Security in One Platform
When the network slows down or suspicious traffic appears, time is lost figuring out where to look. Plixer One lets you trace performance issues, detect abnormal behavior, and confirm what happened from the same data, in one workflow.
Download the Plixer One Data SheetPlixer One Core
Plixer One Core is the foundation of the Plixer One Platform, equipping customers with full-scale observability across an ever-evolving hybrid network environment with forensics and insight to always know the network’s health, understand what’s happening, and swiftly get to the root cause of events affecting the network in the datacenter, cloud, branch offices or across SD-WAN.
Download the Plixer One Core data sheetPlixer One Enterprise
Plixer One Enterprise enhances observability using AI and machine learning, helping users truly grasp their network’s state, traffic flows, and performance while identifying potential risks early. The platform features comprehensive capabilities for Network Performance Monitoring and Diagnostic(NPMD), network planning, research and executive reporting, and MITRE ATT&CK®-aligned Network Detection and Response.
Explore Plixer One EnterprisePlatform and Cloud Support
Plixer One runs in the datacenter, public/private cloud, VMs, containers, and on an appliance.