More and more people are working from home. Now, organizations need a way to understand the role a remote workforce plays in their network performance and security posture. Fortunately, with network traffic metadata, organizations can easily monitor VPN traffic, whether it’s through a split tunnel or no-split tunnel.
Specifically, when organizations collect this information from their VPN and internet firewalls, they gain access to a wonderous amount of information. It ranges from simple network connection details to advanced analytics information like TLS certificate and GeoIP information.
VPN overview
Your remote users likely connect to your network through a Virtual Private Network.
A VPN is an extension of a private network that uses different types of encryption. This allows remote users to log in to a private network securely and retain access to all of the resources that they use on a local connection. But how do you know what your users are doing once they are connected? Are they using too much bandwidth? Are they connecting to non-work-related sites?
Seeing into the VPN tunnel
To show how you can get these details, I’ve set up a lab environment where users connect to the VPN via a Cisco ASA. When I select this ASA in Scrutinizer, I can see the users who are connecting to the network via VPN. This report indicates the heaviest users by volume of traffic.
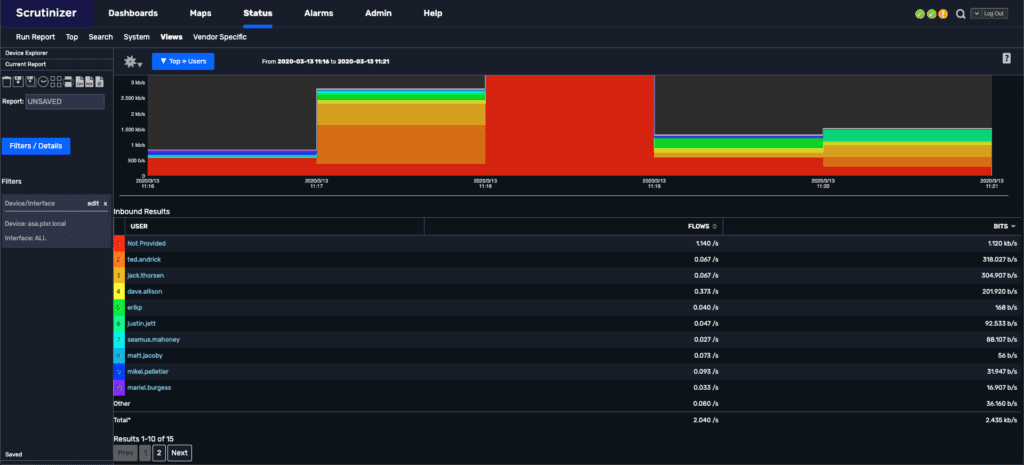
From this report, there are a few things to consider. If your users are connecting to your VPN in a no-split way—meaning that all of their traffic is passing through the VPN connection not just local traffic—then all you need to do is select the username and choose the default report. This will then show you all the traffic associated with that user. This is the best way to monitor VPN traffic. Everything is coming through the VPN.
But if the traffic is split, you won’t see any traffic other than the internal resources requested via the VPN connection. Depending on the security requirements and access of your remote employees, you want to consider the type of VPN connection your users are using. You’ll effectively lose visibility while saving bandwidth. For example, connections like Netflix won’t go through the VPN, but you won’t know about Netflix either.
Getting extra metadata from VPN monitoring
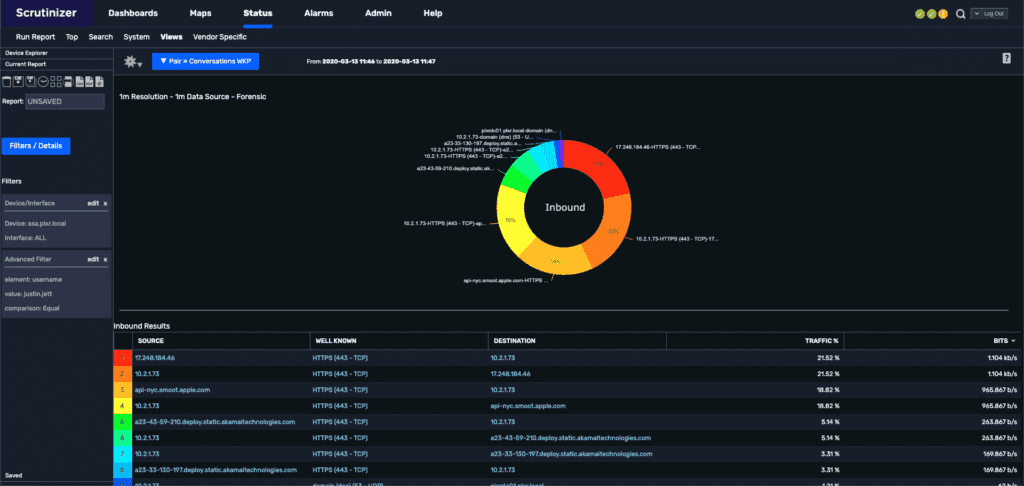
In the above images, there are a few areas to look at. First, our VPN NAT addresses are in the 10.2.1.0 range. This means that for my user, the IP is 10.2.1.73. If I select that IP address, I can move away from our ASA and search any number of exporters that our global, distributed network has access to. This means that I can see information like TLS decryption from our Gigamon appliances, or GeoIP details from Ixia. While this isn’t information you would normally expect by monitoring VPN traffic, it can be very useful, especially as more employees start working outside of the physical office.
Of course, I can’t possibly have recreated all the various lab environments that organizations may have set up for their VPNs. To that end, if your organization has a growing remote workforce and you need better VPN visibility, our engineers will show you how to set it up.
