As a continuation of our Network Security series, I wanted to write a blog on detecting network scans using NetFlow and IPFIX. Since a network scan is often the first step in identifying vulnerabilities on a target’s network it is usually the best place to start in detection. Since there are numerous types of network scans that attackers can use to probe your network it can be a very hard behavior to track. Luckily, if your reading this blog you probably have NetFlow and IPFIX capable devices on your network, which will aid in detection and mitigation of these types of threats.
IPFIX Threat Detection:
Detecting threats on your network such as network scans can be difficult when trying to do so without the help of flow technoligies. With NetFlow and IPFIX, all the information we need is actually being sent to us in basic NetFlow v5! Using TCP flags, our incident response system is able to detect when a user is scanning your network and is even able to alert you when it finds these types of behaviors! You can see some of our threat detection algorithms in the image below. Since there are tons of different scans, I will go over what I see as the most common, the SYN scan.
Network scan detection through IPFIX:
A SYN scan (also known as half-opened scan) is a TCP scan in which the network scanner will generate a SYN packet to a particular host/subnet and if a destination port is open the target will reply with a SYN-ACK. At this point the scanner will respond with RST, never creates the full TCP handshake; they didn’t need to create the full handshake anyway because they already found what they wanted; they now know that whatever port(s) they scanned are opened or closed. From here it’s as easy as looking up specific operating system vulnerabilities for certain ports and executing them. As you can see this type of attack could cause quite a lot of problems on your network. Being able to detect a behavior like this is what sets NetFlow and IPFIX apart from other network monitoring technologies.
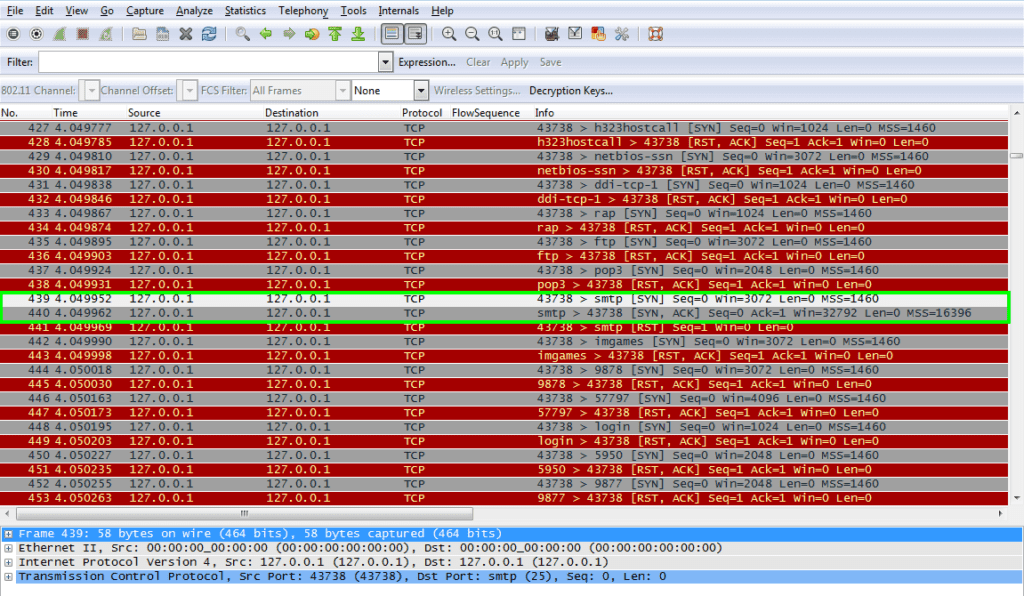
The biggest problem when using other technologies such as a packet capture, for instance, is that you are going to have a lot of data to go through to actually get to the root cause of the problem, whether it be a malicious scan or a miss-configured application on your network. You can see from the image to the left, which shows a network scan I started against myself,
you need to be in the right place at the right time to catch them, since packet capture probes are not usually deployed everywhere on your network (unlike NetFlow and IPFIX).
Feel free to give us a call in support if you need any help detecting network scans, trojan malware, or advanced persistent threats!


