Education
See who is connecting, what they are using, and where performance and security issues start across campus and remote learning.

Importance of Network Visibility for Education
Educational environments are becoming more complex as institutions expand digital learning, adopt cloud platforms, and support a growing number of connected devices across campus networks and remote settings.
As this ecosystem evolves, IT and security teams need clearer insight into network activity to maintain performance and protect sensitive data.
Expanding Digital Learning Environments
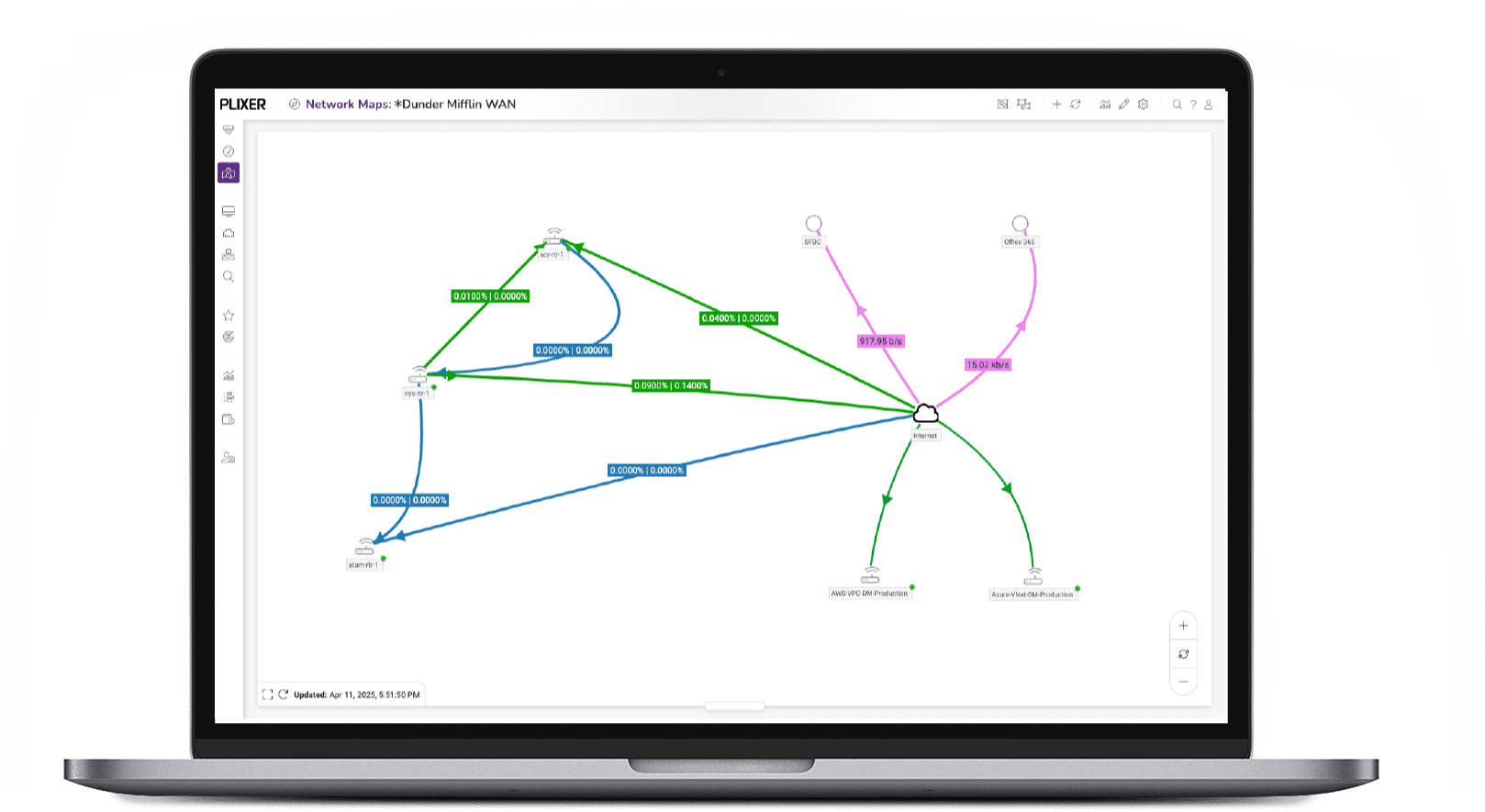
Modern educational institutions now operate across distributed networks that extend beyond campus boundaries. BYOD programs, cloud learning platforms, and remote access have increased network traffic and expanded the attack surface, making it harder for IT teams to understand how systems and devices interact.
Clear visibility into network and device activity helps ensure reliable connectivity, supports flexible learning models, and allows teams to quickly identify performance issues or suspicious behavior.
Rising Security and Compliance Demands
K–12 districts and higher education institutions must monitor large numbers of devices and applications while protecting sensitive student and faculty information. Data moves constantly through learning platforms, collaboration tools, and administrative systems, all while cyber threats targeting education continue to rise.
Supporting Performance and Digital Transformation
As institutions adopt new instructional technologies, hybrid learning models, and cloud-based platforms, preserving consistent performance across systems becomes critical. Even minor disruptions can affect instruction, testing, and campus operations.
Insight into system performance and usage trends allows IT teams to plan capacity, identify bottlenecks, and resolve issues early, delivering reliable digital experiences as technology environments continue to evolve.
Stronger Protection of Sensitive Data
Understanding how data moves across the environment makes it easier to spot unexpected access paths or data transfers. This supports tighter controls around patient information and limits exposure during security incidents.
Benefits of Plixer for Education Institutions
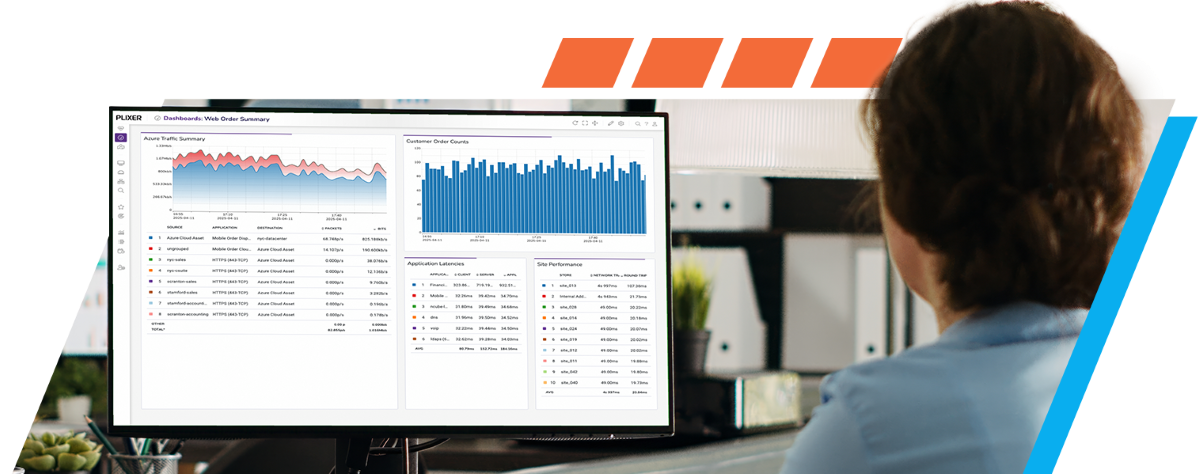
Visibility
Gain full network visibility into every digital interaction, conversation, and device.
Enhance educational experiences and campus operations with in-depth insights that can identify potential threats from both internal and external sources.
Security
Maintain student privacy and support educational data regulations while improving response to emerging cyber threats.
Access to detailed activity data allows security teams to investigate concerns more efficiently and respond with confidence, helping reduce risk across the institution.
Compliance Assurance
Stay ahead of evolving educational regulations and meet compliance requirements with ease.
Use forensic analysis for context with Endpoint Analytics combined with NAT reports to handle information requests and minimize risks related to compliance.
Predictive Planning
Plan capacity for changing educational needs, technology upgrades, and e-learning expansions.
Anticipate both external and internal network behavior changes to adapt smoothly and ensure uninterrupted, secure learning.
Anomaly Detection
Quickly identify anomalies that could impact educational quality or campus safety.
Customize alerts with thresholds that meet the specific requirements of educational environments.
Device Discovery and Risk Scoring
Assess endpoint risk to safeguard against internal and external vulnerabilities in educational settings.
Ensure secure operations while addressing the unique device landscape of educational institutions, crucial for monitoring and managing student-related activity and risk.
Cloud Visibility and Detection
Extend visibility into cloud environments, essential for managing educational technology and supporting safe use of cloud-based tools.
Securely manage cloud-based educational tools and initiatives, with an emphasis on detecting internal threatsand policy violations to support safe digital learning.
Policy Validation and Compliance
Align network and network security policies with educational standards and regulations.
Efficiently detect and address policy violations to maintain compliance and educational integrity.
Need Help Deciding?
Reach out to our team of experts. Our goal is to help you find the best solution for your IT challenges.
Schedule a Demo
What to expect
Buying technology is often complicated and exhausting. We like to make it easy and straightforward. Here’s what to expect from our process:
We’re here for you throughout the process and want to make this as smooth and as thorough as possible.
