
Why Root Cause Is Often Found Outside the Alert That Fired
Often, an alert feels definitive. A threshold was crossed; something measurable went wrong at a specific place and time.
Read MoreInsights, updates, and technical deep dives from our team

Often, an alert feels definitive. A threshold was crossed; something measurable went wrong at a specific place and time.
Read More
SD-WAN was supposed to simplify the network. In many organizations, it did the opposite. Abstracted tunnels, dynamic path selection,
Read More
Encrypted traffic is now the dominant mode of communication across enterprise networks. TLS and HTTPS protect users, safeguard sensitive
Read More
Encryption protects data privacy, but it also hides intent. Every day, more of the world’s network traffic moves under
Read More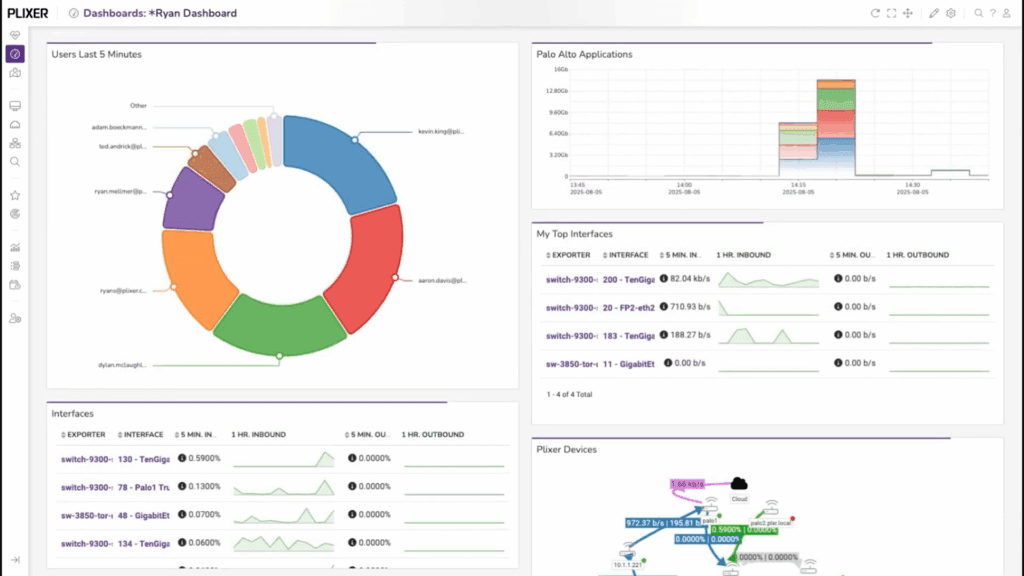
Dashboards are the fastest way to turn network data into something you can act on.Instead of scrolling through reports
Read More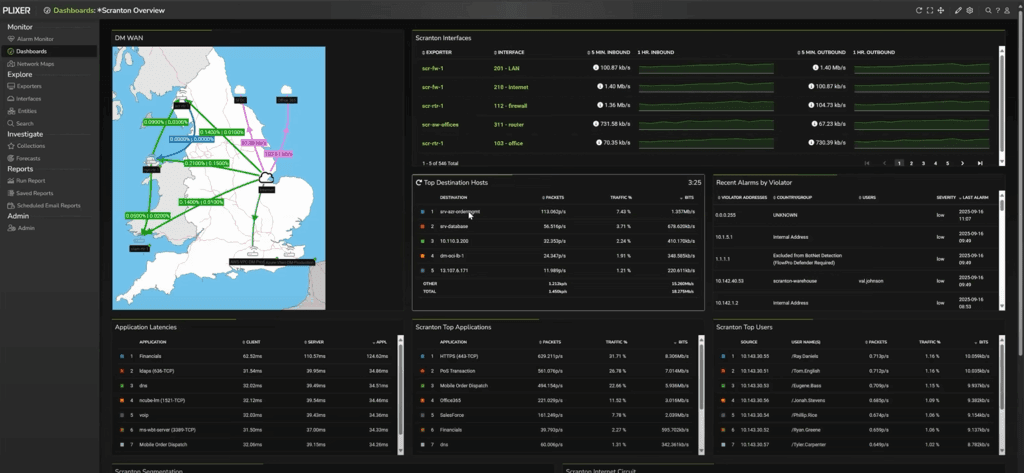
Dashboards give NetOps teams fast situational awareness. But when performance degrades or QoS policies fail, you need to drill
Read More
In today’s IT environments, network and security teams face ever-growing challenges in maintaining visibility, efficiency, performance, and security across
Read More
Modern networks are sprawling, dynamic ecosystems that power nearly every business function. And to keep these systems running smoothly,
Read More
As traditional perimeter-based defenses prove inadequate against today’s cyber threats, Zero Trust offers a flexible and comprehensive model grounded
Read More
Network infrastructure generates a constant stream of IP traffic, and understanding how that traffic moves is essential for maintaining
Read More