Most cyber security professionals are largely concerned about the malware and bad actors that are attempting to break through their security defenses. However, there is a seemingly “good actor” already inside the company that is taking corporate information from the computers it is installed on. If you were aware of what it was taking, you may not agree to it.
Questions:
- Does your company have Windows 10 machines on the network?
- Does your company use Plantronics headsets?
- Do your employees use Linkedin?
- Is there an antivirus software deployed such as McAfee?
If you answered yes to any of these questions, you need to be aware of a practice called DIGing (Dubious Information Gathering). All of the companies listed above are taking information off of computers and uploading it to a server on the Internet for big data analytics.
What Information are they Taking?
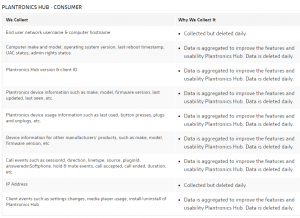
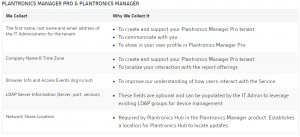
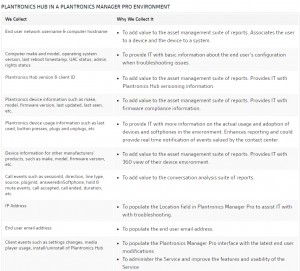
In the recently published paper “Companies You Trust are Stealing Your Data”, we outlined a few companies that are engaged in DIGing. For example, Microsoft Windows 10 takes information related to contacts, the calendar, text and touch input (I.e. a key stroke logger ?), location information and more. Depending on the version installed, Plantronics constantly uploads to their cloud storage, information pertaining to the username, the computer host name, IP address, call accepted events, call ended events, call duration, etc. It is all listed on the Plantronics web site. Below are some screen captures of what they are capturing from their customers computers:
McAfee is another company that uploads information from desktops. They use a method of DNS tunneling which ensures connectivity incase the machine is blocked from the Internet.
You can’t turn it off
With Microsoft, you can disable most of the phone home behavior but, the free OS will still send information back to the mother ship unless the paid version is purchased. With Plantronics, you can’t turn it off although, the contact at Plantronics I spoke with said they plan to return the disable option in a Q4, 2016 release. We found no option to turn off the DIGing behavior in the McAfee software.
Who Gave Them Permission?
In most cases, when the software was installed, we gave them permission when we clicked the ‘Accept’ button after reading the End User License Agreement (EULA). The EULA outlined that information would be taken from the computer and uploaded to the cloud. Details on the information however may not have been clear. Regardless, the EULA was accepted and permission was granted.
How Can You Stop the DIGing
The options for stopping the DIGing behavior are limited. The software can be uninstalled. However, depending on the EULA, your data may not be deleted. Plantronics states that they will delete it in 30 days upon request. Another option is to use a network traffic analyzer to determine the Fully Qualified Domain Name (FQDN) that the software is sending the information to. Once you know the FQDN, the request for it can sometimes be redirected at the DNS. This effectively, blocks the transfer
Their DIGing Could Hurt You!
Plantronics collects LDAP Server Information which includes server details such as the port the server is running on and the version. If the Plantronics customer data is stolen, certainly this could help a hacker as they would have details regarding how users authenticate onto the network. They also collect username, computer host names, first and last name as well as email addresses. I can’t imagine a hacker that wouldn’t be interested in these details for targeted phishing attacks.
Helpful Vs. Over Reaching
We agree that software vendors can benefit by collecting some information from end users regarding how the software is performing. Some vendors however might be taking a bit too much information and could be “over reaching” on the boundaries regarding what is really necessary. To learn more, download our white paper “How Companies You Trust Steal From You“.