I’m excited to announce that the Alarms tab in our next version of our network threat detection solution will include index enhancements. Specifically, the “Threat Index” is a value placed on any host that our propriety threat detection algorithms mark as suspicious. The concept of a threat index or security index is not new. It has been around for many years and is leveraged by different industries such as the Weather Channel. However the way we employed the threat index is unique in our industry.
Monitor for Threats
We added threat detection to our NetFlow Analyzer several years ago. Our strategy for detecting malware is a process where flows are passed through a series of algorithms which look for odd communication patterns. Suspicious connections are identified by looking at behaviors in the flow ratios related to TCP flags, port volumes, comparing activities to stored baselines and other proprietary forensics. The algorithms violated carry different weights and will increase an individual host’s Threat Index. If the index reaches a threshold prior to events aging out, notifications are triggered.
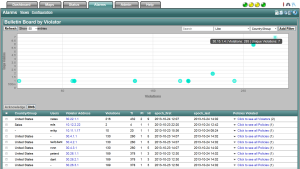
In the image below, the TI is the threat index followed by the policy index (PI) and the host index (HI). All of which will be explained in time.
Threat Index
Keep in mind that the threat index for a host is a moving value because individual events age out over time. For this reason, an IP address carrying a threat index must reach the configurable threshold within a window of time (e.g. 14 days). In other words, the same events that increased the threat index are also aging out and when that happens, the threat index value will drop. Using this method, it is possible for infected hosts to “fly under the radar” however, here’s something to keep in mind. Most large enterprises agree that there is more than one infection on the network at any given time. The malware might be camping out waiting for instructions from the botnet. If the malware doesn’t talk, chances are nothing on the market today – firewalls, IDS, antivirus, etc. will catch it. So how will we?
Detect Exfiltration
Our strategy is to enhance the customer’s existing threat detection methods either by forwarding our events to another solution or by receiving the events from a third party. By combining traditional deep packet inspection (DPI) malware detection methods with the behavior monitoring methods employed by our NetFlow Analyzer, all the events across platforms can push up the threat index. The goal is to identify ex-filtration of sensitive information and if configured, stop the transaction.
Trying to uncover and eradicate every piece of malware that snuck into a company is like trying to clean and wipe out every germ that exists in a hospital. It simply can’t reasonably be done. For this reason, we need to put in place methods that uncover real ex-filtration while living with a few false positives created by normal end user behaviors. The threat index method anticipates false positives and allows the real threats to rise up and get your attention.
