Good news: Solera IPFIX support is available in our IPFIX reporting solution. This is no surprise as Flow Analysis (NetFlow and IPFIX) continue to gain popularity in several key areas of many IT security programs:
- Data investigation on the source or perpetrator of the threat (i.e. who did what to whom, when and where)
- Merge with other data sources to gain greater contextual information surrounding the details of the malware
- Host Reputation look ups
For those of you who need to get this setup fast, here are the instructions that we got from the documentation.
To create an IPFIX export action, you must have an IPFIX collector on your network. The IPFIX files that DeepSee produces are IPFIX (NetFlow) v.10-formatted.
a. Select DeepSee > Actions.
b. Click New.
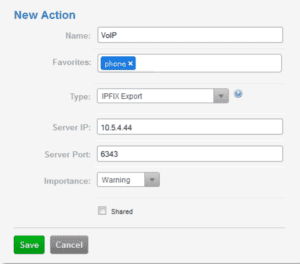
c. The New Action dialog box is displayed.
- Name—Type a name for the IPFIX export.
- Favorites—Type the name of one or more existing favorites.
- Type—Select IPFIX Export.
- Server IP—Specify the IP address or hostname of the IPFIX collector.
- Server Port—Specify the port number that the IPFIX collector uses.
- Shared—Select to make the action viewable to everyone who has access to this appliance.
d. Click Save. When network traffic matches the favorite, the entire flow is exported to an external IPFIX collector, and an alert appears on the Alerts page.
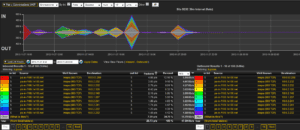
Once the flows are coming into the NetFlow and IPFIX collector you can take advantage of the IPFIX Reporting.
Solera DeepSee Appliances are highly scalable and pre-configured with DeepSee Software for turn-key deployment. They claim to deliver complete network visibility of advanced threats, malware and zero-day attacks. Since the appliance has access to 100% of the packets, we could see Solera export portions of the packets in IPFIX sometime in the future. It is nice to see another security company recognize that NetFlow and IPFIX need to play a considerable roll in their security and threat detection offering.
If it’s syslog reporting you need, we can correlate the IPFIX data with the syslogs exported by the Solera appliance by pointing the logs to our Flow Replicator which can act as a syslog to IPFIX gateway.