Are you looking for a solution for Bro Log Reporting? This is a post on how we ended up with a really great solution for reporting, trending and searching through Bro logs by converting them to IPFIX.
What is Bro
Developed by Vern Paxson, the Bro solution is often compared to a Network intrusion detection systems (NIDS) but, it is really much more than this. Bro can be used for collecting network measurements, conducting forensic investigations, traffic base lining and more. It has been compared to tcpdump, Snort, NetFlow, and Perl (or any other scripting language) all in one and it is released under the BSD license.
Bro’s Claims to Fame
- Adaptable: Bro’s domain-specific scripting language enables site-specific monitoring policies.
- Efficient: Bro targets high-performance networks and is used operationally at a variety of large sites.
- Flexible: Bro is not restricted to any particular detection approach and does not rely on traditional signatures.
- Forensics: Bro comprehensively logs what it sees and provides a high-level archive of a network’s activity.
- Commercially Supported: Broala offers consulting, training, and custom development by the creators of Bro.
- In-depth Analysis: Bro comes with analyzers for many protocols, enabling high-level semantic analysis at the application layer.
- Highly Stateful: Bro keeps extensive application-layer state about the network it monitors.
- Open Interfaces: Bro interfaces with other applications for real-time exchange of information.
- Open Source: Bro comes with a BSD license, allowing for free use with virtually no restrictions.
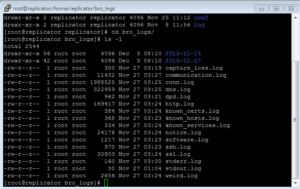
In short, its open source network analysis framework provides IDS capabilities without relying on traditional signatures. During its normal course of operations, it creates numerous logs that can represent network traffic is different ways. For example: some logs contain details on http traffic, SSL certificate details, connection state, and much more. Take a look at the list of log files it dumps details into:
What Bro Logs Look Like
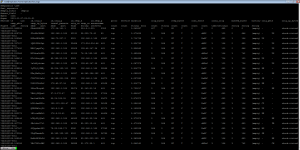
Each log is delimited (in this case a tab). This makes it easier to write scripts to analyze and monitor the network for specific events. Users can configure Bro to output all types of information. Notice in the example below we see entries containing details on the source and destination IP address, ports, protocol, bytes, etc. This log is starting to almost look and smell like NetFlow but, it’s missing a few elements and it includes a few new ones.
How to Convert Bro Logs to Flows
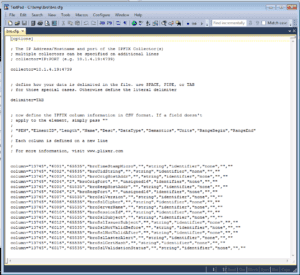
Using Scrutinizer’s IPFIX utility in file follow mode, users can convert their Bro logs into IPFIX by custom defining their own elements and templates. The IPFIX utility will then watch an individual file for new events, convert those events to flows and send them to the collector. Multiple instances of the IPFIX utility can be used to monitor different files simultaneously. Below is an example of the IPFIX utilities cfg file:
Bro Logs converted to Flows
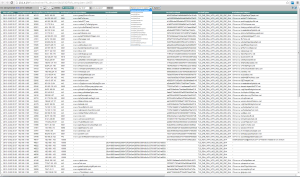
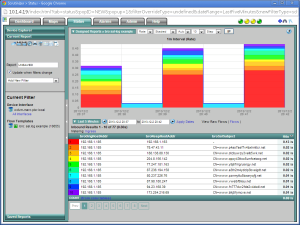
Once the converted logs to flows have been collected by Scrutinizer, Bro Log Reporting can take place.
Bro Log Reporting
Once the reports are run, filters can be added and thresholds can be set to watch for specific events or patterns. Ultimately, notifications can even be sent.
So, if you are interested in Bro Log Reporting – now you know where you can find it.