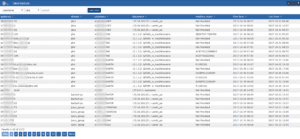
Correlating NetFlow with RADIUS Usernames to improve context security awareness is something we have done for several vendors including Cisco ISE, Microsoft Network Policy Server, Forescouts CounterACT and others. Even with all of these supported, we still get approached with yet another RADIUS system that the customer wants us to pull usernames from and of course they want them correlated with the IP addresses found in the NetFlow and IPFIX we collect.
The good news is that we can do it. The other good news is that it’s relatively easy to do but, it does require some work. The caveat is that it will have to be assessed on a case by case basis. Most of the time, free solutions like FreeRADIUS and OpenRADIUS and commercial solutions like Cisco Prime will log the data to a file which is a big help.
In the logs we have reviewed, we’ve noticed that most are in a unique format. Some are one line in quoted CSV, others are multiple lines. And others like Cisco Prime don’t have all the details we need unless the log is set to trace mode. The kind of log we prefer to work with is called the “accounting log”. Which needs the following data in order for us to add username support more broadly:
- The client’s IP Address, FRAMED-IP-ADDRESS: Typically, the IP address of the dial-in host is not communicated to the RADIUS server until after successful user authentication. Communicating the device IP address to the server in the RADIUS access request allows other applications to take advantage of that information.
- User-Name: This is the username making the request regardless of whether the authentication is pass or fail. If we want to narrow it down, we could only export a flow if authentication passes via the Account-Response event which should be in the log.
- The Log must contain both the request and response requests
How it will Work
We use software that provides a modified tail mode which will watch an accounting log. It provides the intelligence to understand variations in the log format (E.g. single vs. multiline). It then extracts the data out. This process has to be done on a case by case basis in order to add support for a customer’s unique RADIUS solution.
Questions we get Asked
Q: Can Scrutinizer integrate with our RADIUS server?
A: Most likely. Can we have a copy of your RADIUS accounting log?
Q: Can Scrutinizer support the syslogs our RADIUS server can send?
A: Most likely. Can we get a sample of these syslogs?
Q: Our solutions sends data as Microsoft eventlogs. Can Scrutinizer support it?
A: Yes, our current release recognizes those eventlogs.
If you don’t need all of the technical detail, the bottom line is if you are ready to start correlating NetFlow with RADIUS usernames, we can help. Reach out to our team and be ready to share some sample data if we are being asked to support something we haven’t seen before.