EDIT 5/30/18: There is a newer version of this article available.
In order to configure Cisco ISE NetFlow, we’re going to take advantage of Scrutinizer’s API (Application Program Interface) by enabling ERS (External RESTful Services), on the ISE appliance.
You probably already know about Cisco ISE (Identity Service Engine) profiling using the NetFlow Probe. However, the ISE appliance can be integrated into your Network Response System, in order to give you contextual details into who is generating traffic on your network.
First, enable ERS and create a new user with ERS Admin, ERS Guest, Super Admin, and System Admin permissions, as these (and only these) privileges will allow queries.
Here is the guide for enabling ERS for ISE 1.4, ISE 1.3 and ISE 1.2.
To test your configuration outside of Scrutinizer, use POSTMAN to do a GET, using this URL:
https://%5BISE_SERVER%5D/ise/mnt/Session/AuthList/null/null
*tip: when using POSTMAN, first navigate to the server with your browser, tell chrome it is OK to use a bad certificate and leave that window open.
Next step is to add the user you just created in Scrutinizer, via command line:
# ./plixer/scrutinizer/bin/scrut_util.exe -ciscoisenode add –host [host] –port [port] –user [user] –pwd [password]
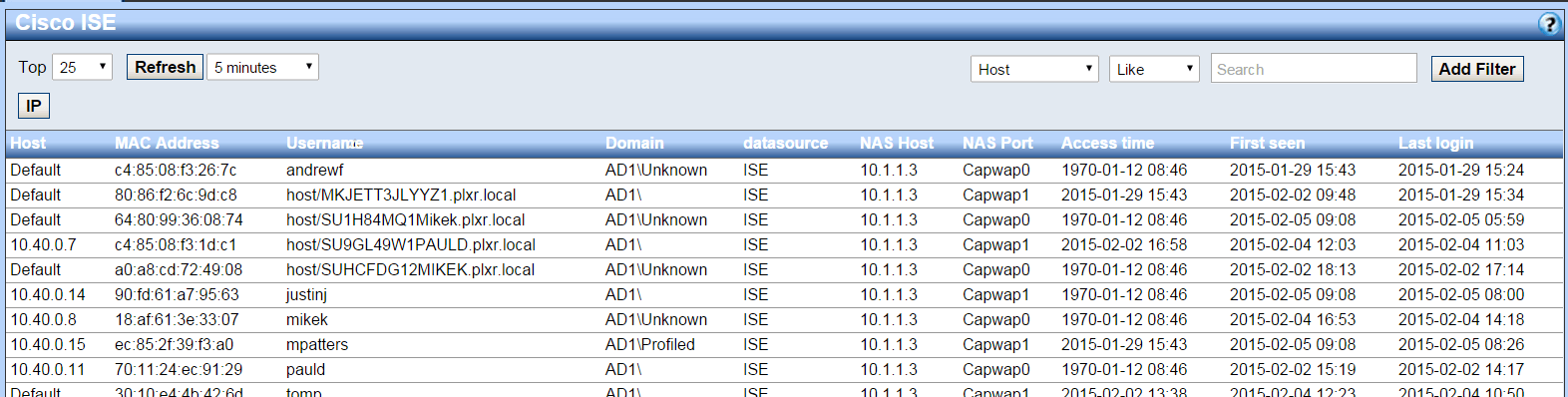
That’s it. For all your hard work, Scrutinizer will poll the ISE appliance every 5 minutes to get updated username information. By going to Status>Views>Cisco ISE, you will see a list of users with details like username, IP address, MAC address, access time and more:
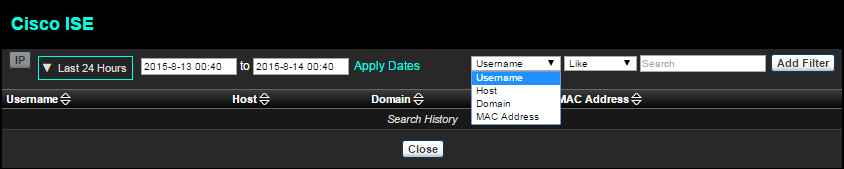
Similarly, you can search the entire database for username, host, domain name, or MAC address:
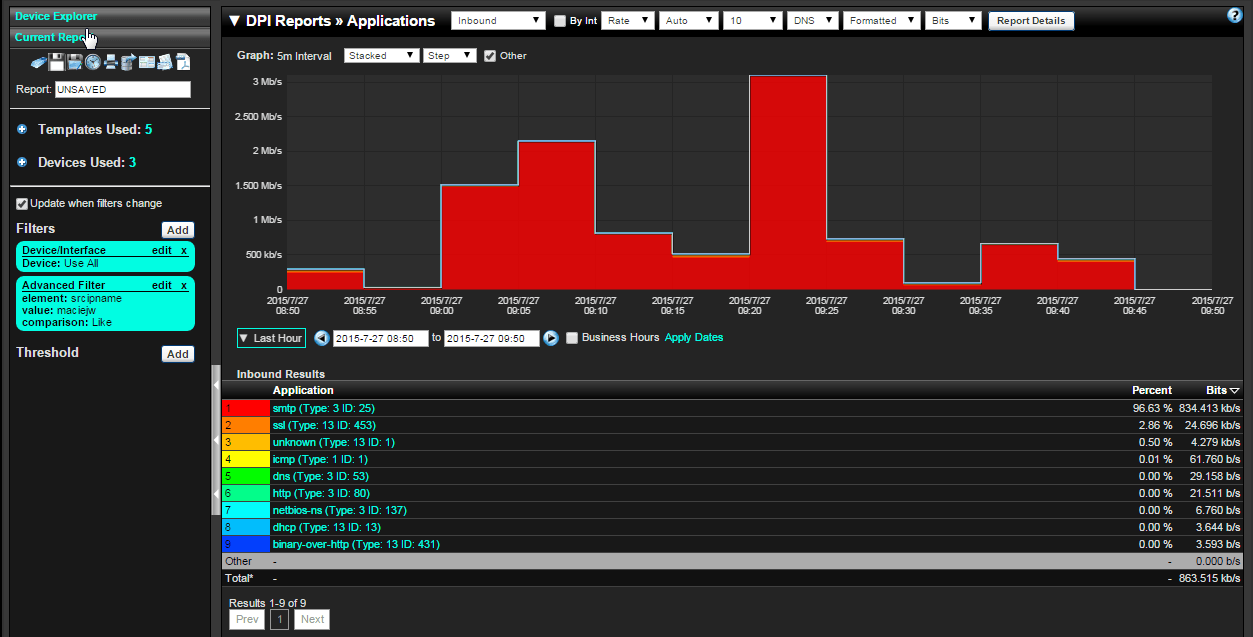
If you’re already investigating a report, you can click on a host and select the Cisco ISE option from the “Other” menu to quickly figure out what user is responsible for this traffic. Let’s see what applications Maciej is using:
Available on your Scrutinizer appliance, virtual and/or hardware.
If you have any questions, need help with your Cisco ISE NetFlow configuration, or would like to add username reporting to your incident response system, please contact Plixer.