We will be demonstrating our new Cisco ASA FireSIGHT reporting at CiscoLIVE! in Berlin Germany this month. This appliances provides the deepest and richest detailed information that we have seen from any firewall. Our customers are going to love it.
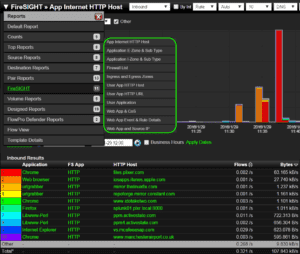
There are dozens of default reports that will work with this export and we added almost another 11 that are specific to the unique elements gathered from FireSIGHT. Users can leverage the Report Designer to create hundreds more, especially if they enable additional elements in the configuration file.
To get this working two routines have to be followed:
- The types of events the eStreamer server is able to transmit to client applications must be selected. To do this, Navigate to System > Local > Registration, click on the eStreamer tab and under eStreamer Event Configuration menu, check off what you want sent to the client.
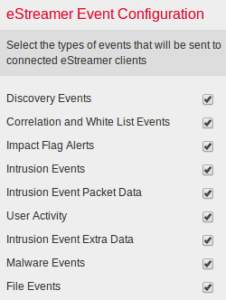
NOTE: FireSIGHT / eStreamer is not exporting NetFlow or IPFIX. The data is gathered via an API. - The Scrutinizer client for eStreamer (Event Streamer) must initiate an SSL-enabled TCP connection with the eStreamer service (FireSIGHT Management Center). The eStreamer server will then respond by initiating an SSL handshake with the client. As part of the SSL handshake, the eStreamer server requests the client’s authentication certificate, and verifies that the certificate is valid. Scrutinizer then starts the eStreamer service and then data exchange can take place. What is really cool about this is that Scrutinizer can be configured to request specific data from the FireSIGHT system. There are well over 100 unique elements that could be exported but, the default setting is to export a dozen or so on top of the typical NetFlow/IPFIX tuple. The user can choose what they want to export but, selecting too many elements can cause 1 BIG Problem.
Even URL can be exported from FireSIGHT:
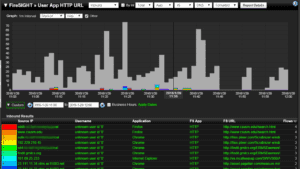
If you have several Cisco ASAs setup with the FireSIGHT server, Scrutinizer will be receiving the data from the FireSIGHT IP address. Within the FireSIGHT export, it does tells us the individutal IP addresses of the ASAs that are sending the data. However, it is not the same IP address that is exporting the NetFlow Security Event Logs (NSEL). Although it is sort of a juggle to keep track of all the IP addresses, the richness of the data should make it all worth the trouble. The application, end system and destination data available will certainly make the Cisco ASA an attractive solution to customers who want visibility into Internet bound traffic.
If you would like to evaluate this new Cisco ASA FireSIGHT reporting, just reach out to our team and ask for an evaluation. Our system engineers are also available to evaluators that need help with the configuration.