Plixer
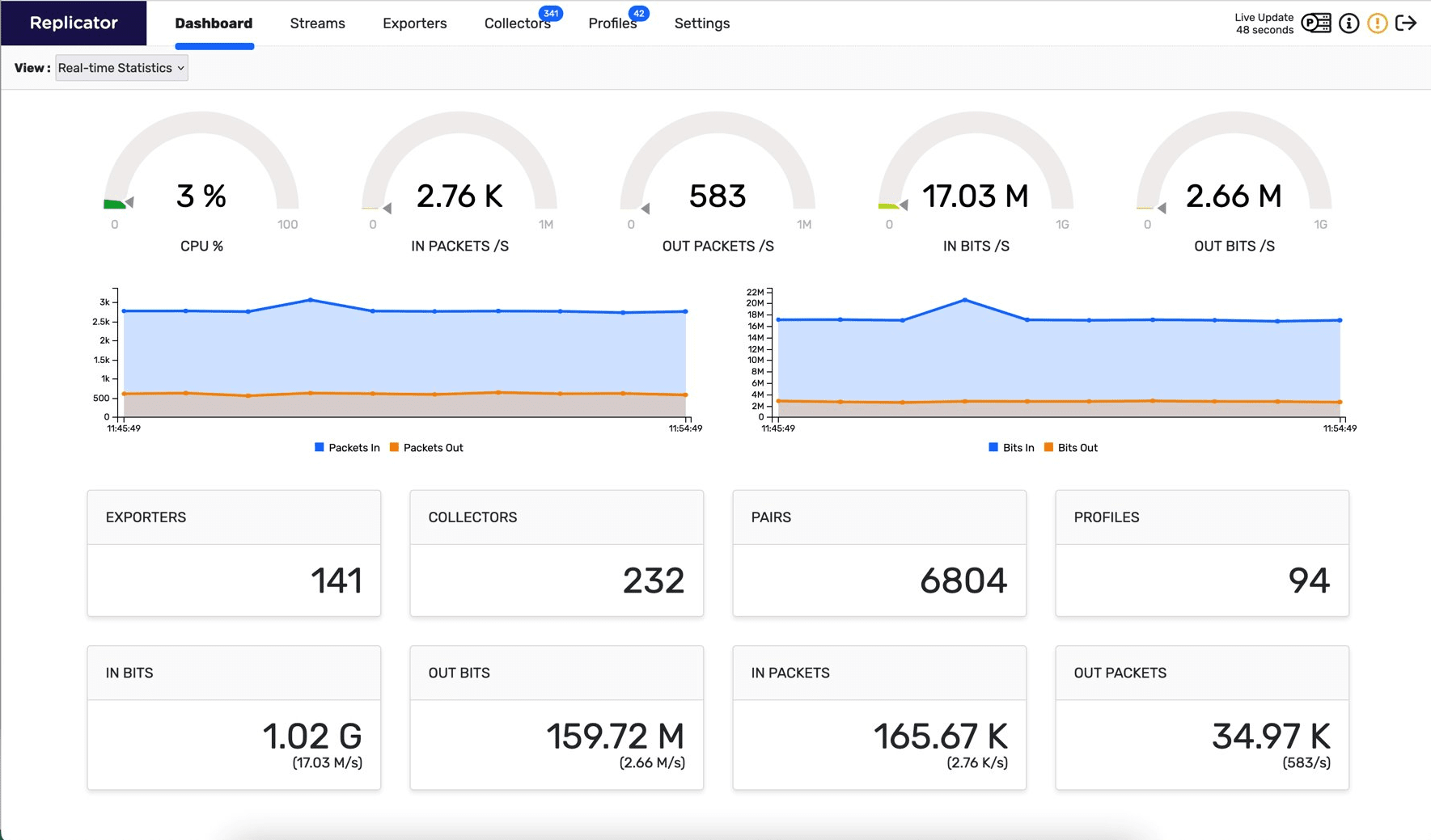
Replicator
Streamlined UDP Replication for Enhanced Data Analysis
- Centralized Data Management: Streamline and centralize your network data for enhanced visibility and simplified management.
- Balanced and Efficient Routing: Optimize network performance with intelligent data distribution to key analysis tools.
- Seamless Network Integration: Ensure smooth data handling and minimal disruption within your existing network infrastructure.
Enhance your data analysis capabilities. Plixer Replicator replicates and channels UDP data streams from exporting devices to collection systems, efficiently boosting your security and management tools’ performance. This solution not only improves the efficiency of your monitoring tools but also optimizes your infrastructure, ensuring high performance in complex network environments.
Dynamic Data Forwarding
Plixer Replicator takes a singular UDP traffic stream and routes it to multiple endpoints. This unique capability ensures you get the most out of your Plixer One Platform solutions.
High Availability, High Efficiency
Plixer Replicator augments your Scrutinizer setup. With its smart distribution and adaptive load balancing in the face of data surges, your data becomes manageable.
Streamlined System Updates
Expand your security and network monitoring effortlessly. By rerouting an additional UDP metadata stream through Plixer Replicator, you bypass the need for intricate switch or router configurations, protecting infrastructure performance and reducing overhead.
Thwart Hacker Obfuscation
Hackers might attempt to erase their presence, but Plixer Replicator puts a stop to it. By dispersing logs and data across varied repositories, it ensures that any malicious effort to delete traces would have to overcome multiple barriers.

