Apparently there are quite a few YAF IPFIX deployments out there. We recently had to test this software for a customer. YAF stands for Yet Another Flowmeter which promotes the use of SiLK for some rudimentary threat detection. Flow Analytics(TM) can be used for more sophisticated network threat detection. YAF can be placed off a spanned switched port and used as a NetFlow probe to improve network traffic monitoring; however, the metrics collected are not nearly as sophisticated as the nBox.
The configuration of YAF is pretty straight forward.
sudo yaf –in eth0 –live pcap –out 10.1.4.66 –ipfix udp –ipfix-port=2002 –stats=300 –mac –idle-timeout=60 –active-timeout=60 –udp-temp-timeout=300 –force-read-all –silk –observation-domain=42 –flow-stats –delta –ingress=1 –egress=1 –max-payload=128 –export-payload –udp-payload –entropy –applabel –p0fprint –fpexport
Some options above are optional, others are not. For instance, using “–silk” is very important due to how that effects the export.
Descriptions of each option are available on the YAF web site. An interesting piece of information is that like many security appliances (e.g. SonicWALL, Cisco ASA) that support IPFIX, YAF supports bidirectional NetFlow this was evident when we saw things like octetDeltaCount and octetDeltaCount_rev (rev = reverse) in the same template. Other unique elements included:
- droppedPacketTotalCount
- exportedFlowRecordTotalCount
- exportingProcessId
- flowAttributes
- flowEndReason
- ignoredPacketTotalCount
- initialTCPFlags
- octetTotalCount_rev which may support RFC 5610, I need to look at it a bit more with our developers
- silkAppLabel
- tcpSequenceNumber
- unionTCPFlags
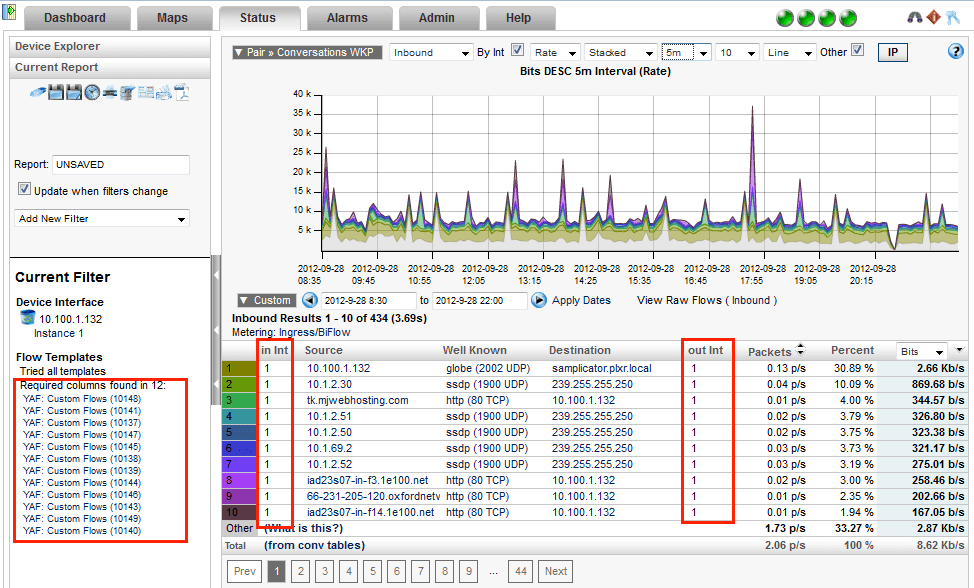
All of which can be reported on using our Report Designer. The report designer allows customers to select any template from any device, select the elements and of course, group, orderby, sum, count, average, etc. on any column for trending. Consider it a sort of Crystal Reports for flow templates. Anyway, a YAF reporting example can be seen below.
As you can see above, our configuration caused an export of 12 templates! There is nothing wrong with this and the reason for it is the topic of perhaps another blog. For now, understand that it demonstrates how the IPFIX industry is evolving.