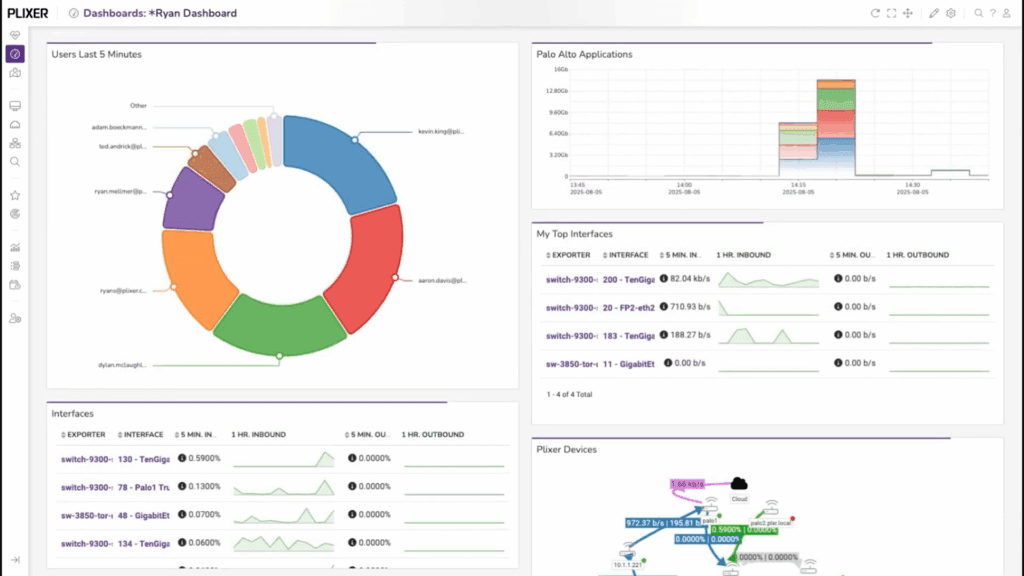
How to Build Custom Dashboards in Plixer One
Dashboards are the fastest way to turn network data into something you can act on.Instead of scrolling through reports
Read MoreCategory: NetFlow Reporting
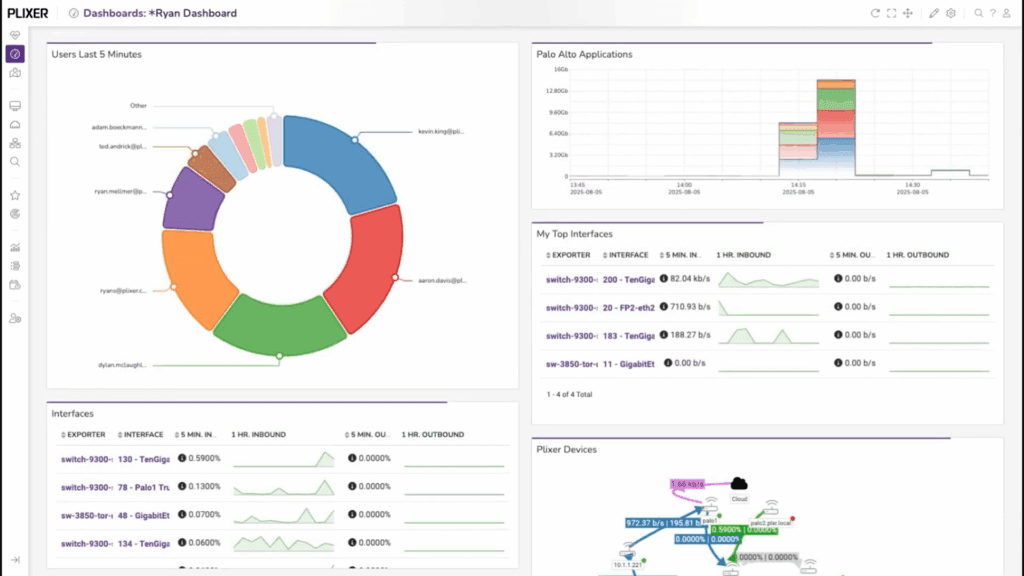
Dashboards are the fastest way to turn network data into something you can act on.Instead of scrolling through reports
Read More
As I was visiting customers onsite last week, a few of them asked me if we support Cisco TrustSec
Read More
UPDATE: The information below applies to version 17.x of Scrutinizer. If you are on a recent version, after you’ve
Read MoreAccording to Gartner, when it comes to context-aware security, the most commonly cited context types are location and time.
Read MoreOur IT department recently went through the process of evaluating Splunk competitors such as Elasticsearch and a couple of
Read MoreAre you looking for Meraki NetFlow Support? We recently came across this flow export and ran it through our
Read MoreWe frequently receive inquiries regarding the availability of APIs (Application Programming Interface) for our Advanced NetFlow reporting solution, so
Read MoreAs a continuation of our Network Security series, I wanted to write a blog on detecting network scans using
Read MoreIf you have another network management solution in place, and need (or just want) NetFlow integration support to include
Read MoreMikroTik NetFlow support and configuration is a two-step process that can be achieved in a Command Line Interface (CLI)
Read More